In 2021, a door that seemed to have been sealed shut by time forever suddenly swung open after nearly half a century of silence.
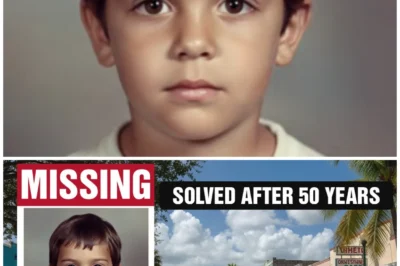
The disappearance of Judith Anne Mercer, the woman who walked out of her ordinary life in California in 1974 and vanished without a trace, finally began to speak.
For decades, her family waited in despair.
files gathered dust in storage, and the truth lay buried beneath unfinished assumptions and unanswered questions.
Only when modern science reached out to those old pieces of evidence, did fragments of the past begin to resurface, cold and unrelenting, forcing every old explanation to collapse.
Today, I’m taking you straight into the heart of a tragedy that has stretched on for nearly 50 years.
How Judith Anne Mercer disappeared.
What really happened in that deadly gap of time? And who holds the key to the secret that was hidden for decades.
This is not just a missing person case.

It is a chilling testament to the fact that the truth can wait patiently longer than any human being.
You are the reason these forgotten stories are being told again.
Take a deep breath because right now we are stepping into a journey where the past comes alive and justice has nowhere left to run.
Before we dive deeper into this haunting true story, let us know where you’re watching from.
And if you love journeys uncovering justice buried by time, don’t forget to subscribe so you don’t miss the next cases.
Judith Anne Mercer left her last confirmed location on an ordinary evening in California in 1974 with no sign whatsoever that this would be the final moment anyone would see her.
No public argument, no hurry or panic.
Just a woman around 30 years old finishing her usual tasks and stepping out of her familiar space with a clear plan for the hours ahead.
A wrote that everyone around her considered completely reasonable and safe.
She was last seen going about her normal routine, neatly dressed without any unusual luggage, showing no signs of fear or avoidance of anyone.
Her car left in the right direction at the right time, blending into the familiar rhythm of the area where she had lived and worked for a long time.
According to plan, Judith was supposed to arrive at her intended destination shortly afterward, a personal appointment that was not secret, not suddenly changed, and with no reason to make her vanish from her daily routine.
However, time passed without any indication that she had arrived.
The clock kept ticking through the familiar evening milestones, and her initial absence was explained by very ordinary possibilities, such as traffic, stopping somewhere else, or simply being delayed unintentionally.
As the waiting period stretched longer than expected, the first attempts at contact were made, but yielded no results.
Her phone went unanswered, no return calls, no signal that Judith was on her way, or had changed plans.
Franklin Wade called her, the person waiting for her to return, began to realize that this silence was not like Judith, because she was not the type to disappear without leaving word, especially in situations that had been arranged in advance.
Time continued to pass.
Evening gradually turned into night.
Initial assumptions became less convincing and worry began to replace patients because every minute without news made the possibility of a serious incident harder to ignore.
Franklin tried contacting her several more times, checking the simplest possibilities, asking himself unanswered questions about whether Judith had stopped somewhere and forgotten to report it, whether there was some unusual delay still within control.
But every effort ended in the same result.
absolute silence.
As the night grew late, the feeling of unease was no longer a vague guess, but an undeniable reality.
Because there was no sign that Judith was anywhere along her familiar route, and the prolonged inability to reach her exceeded the limits that loved ones could accept.
The family began waiting in a state of tension, constantly glancing at the clock, constantly checking possibilities, but finding no clue to explain this prolonged absence.
and every passing minute reinforced the single conclusion that Judith had not arrived at her intended destination and had not returned home as she should have.
There was no call to report a delay, no message left behind, no intermediary to convey information, only a prolonged emptiness in communication and an increasingly clear feeling that this was no longer a normal delay.
At a certain point, continuing to wait was no longer a reasonable option because every decision to postpone reporting the matter meant losing more time in a situation where time could be the most critical factor.
Franklin Wade Calder, after weighing what had and had not happened throughout the period of Judith’s absence, made the decision to officially report to the police that his wife was missing, marking the moment when Judith Anne Mercer’s disappearance was no longer a private family concern, but became an officially recorded case, opening a new phase where her absence was deemed abnormal and required intervention from law enforcement.
The missing person report was received as a routine procedure, but quickly forced law enforcement to shift into priority handling mode because even in the first few minutes, the basic data recorded already showed that this was not a random absence that could resolve itself over time.
Information about Judith Anne Mercer’s identity, age, occupation, personal vehicle, and intended route was collected and cross-cheed against the risk assessment criteria in use at the time in which her failure to appear at a predetermined destination, the prolonged abnormal lack of contact, and the complete absence of any notification of a plan change from the victim were considered undeniable red flags.
As soon as the initial report was filed, the person receiving the case had to make a critical decision about how to classify the situation because the difference between a standard missing person case and one with potential danger factors would determine the entire subsequent course of action.
Judith’s personal circumstances were quickly but systematically reviewed, including her daily habits, the stability of her routine schedule, and the likelihood that she would leave voluntarily without notifying anyone.
And this information indicated that the chance of Judith deliberately disappearing was very low.
The complete lack of any sign that she had taken luggage, money, or preparations for a long absence further reinforced the conclusion that this was a situation beyond ordinary delay, forcing law enforcement to assess the case at a higher risk level than most missing person reports received.
During the initial assessment, time was considered the key factor because every hour that passed could reduce the ability to determine exactly what had happened to the victim.
especially in the absence of communication and any direct leads to follow.
On that basis, the decision to open an investigation file immediately was made without waiting any further observation period, marking a major shift from merely recording a report to activating official investigative procedures.
The file was established with all available information while leaving room to add data as new sources or discoveries emerged and the case was classified as requiring urgent handling to ensure all necessary resources could be mobilized promptly.
Determining this to be an unusual missing person case was not based on a single detail, but on the synthesis of multiple factors at once, in which the consistency of the victim’s schedule, the complete absence of contact signals, and the timing of the disappearance all contributed to forming a picture that indicated a real potential risk.
Immediately after the file was opened, investigators were assigned to ensure clear accountability and continuity in handling the case.
Because a single point of contact responsible for followup would help prevent information from becoming fragmented or overlooked in those crucial early hours.
The assigned investigator was tasked with quickly grasping all initial data, identifying what was known and what was missing, and establishing priorities for gathering additional information, from verifying the intended route to checking alternative possibilities that might explain Judith’s absence.
The process of activating the investigation did not occur in a state of panic, but followed a standardized sequence with each step aimed at narrowing the range of uncertainty and turning the incomprehensible absence into a series of specific verifiable issues.
In this context, classifying the case as an unusual disappearance did not mean immediately concluding criminal activity, but reflected a cautious approach to ensure no serious possibilities threatening the victim’s safety were overlooked.
This distinction allowed law enforcement to deploy early investigative measures while keeping the file flexible enough to adjust the direction of handling as new information emerged.
an especially important factor in cases where initial facts are limited.
When the lead investigator officially took over the file, the task was not only to find out where Judith was, but also to determine what had prevented her from appearing at her destination as planned and whether any indication existed of external intervention.
Activating the investigation at this stage reflected the recognition that the victim’s prolonged silence could not reasonably be explained by ordinary causes and that delaying action could lead to irreparable consequences.
From this moment onward, Judith Anne Mercer’s disappearance was transformed from a personal concern into an official case that needed to be resolved, laying the foundation for the entire subsequent chain of actions by law enforcement in their efforts to determine her fate.
The effort to trace Judith Anne Mercer’s last known appearance was launched as a central investigative step to turn her vague disappearance into a specific verifiable point in time and space.
Beginning with a thorough review of all locations where the victim might have been present in the period before contact was lost, investigators focused on identifying the last place where someone else had directly seen Judith, cross-referencing information from individuals who had interacted with her that day and arranging the facts in chronological order to avoid missing any detail.
This process did not stop at recording statements, but also included verifying the context of each contact from timing, distance, lighting conditions to the level of familiarity between the witness and the victim in order to assess whether the provided memory was accurate enough to serve as a basis.
Initial statements were collected systematically with each witness interviewed separately to minimize the risk of information influencing one another while matching and differing details between accounts were carefully recorded for later reliability assessment.
Among these statements, some witnesses confirmed seeing Judith in a normal state of activity with no signs of stress or unease, which helped rule out the possibility that she was trying to evade someone or leaving in a panicked state at that time.
However, this very normality also made tracing more complicated because there was no sufficiently prominent unusual behavior to serve as a clear milestone, forcing investigators to rely on the smallest details to reconstruct the sequence of events.
Each statement was placed within a specific time context, compared with other statements, and with objective information such as estimated travel times between locations to determine whether the described sequence was plausible.
The reliability assessment considered not only the consistency within each witness’s account, but also factors that could affect memory, including the time that had passed, the witness’s level of attention at the time of the event, and their potential to unintentionally infer or add details later.
Statements showing internal contradictions or inconsistencies with other facts were flagged for cautious review, while accounts that matched in timing and circumstances were considered foundational for fixing the last confirmed public appearance of Judith.
As this milestone gradually took shape, investigators began narrowing the time frame of focus, shifting from a broad window to a specific interval where every possibility had to be taken seriously.
Fixing the last confirmed time point was not only to determine when Judith disappeared, but also to create a reference point for all future hypotheses because any event considered related had to have occurred after this point and before she was reported missing.
From that time point, a gap gradually emerged representing the period during which no one could confirm where Judith was or what she was doing.
And this very gap became the focus of the entire investigative effort.
Investigators clearly defined the boundaries of this time gap, marking the starting point as the last confirmed sighting and the ending point as the moment the family realized she had not arrived at her destination and could not be reached.
This gap was analyzed as a space containing every possibility from an unintended accident to deliberate external intervention and narrowing it was seen as the key to understanding what had really happened.
During this process, hasty assumptions were avoided because any premature conclusion could derail the investigation and cause other possibilities to be overlooked.
Instead, the facts were arranged neutrally, allowing the overall picture to emerge gradually based on the overlap of information rather than emotion.
Tracing Judith’s last sighting did not provide immediate answers, but it created an important foundation, transforming her disappearance from an amorphous phenomenon into a structured problem with specific time points and a clear gap that needed to be filled by the next investigative steps.
The construction of a feasible travel route for Judith Anne Mercer was carried out as a highly technical investigative step to transform the established time gap into a specific spatial sequence that could be analyzed, controlled, and progressively eliminate implausible possibilities.
This began with synthesizing all known information about the victim’s daily habits, personal schedule, regularly used routes, and familiar destinations within the California area where she lived and worked.
Investigators did not assume Judith had only one possible route.
Instead, they built multiple parallel route scenarios based on the most geographically and temporally logical paths, including both convenient main roads and secondary routes that might have been used in specific situations.
Each route was analyzed in detail for length, road conditions, traffic density by time of day, and connectivity to surrounding areas, allowing for relatively accurate travel time estimates for each segment in the absence of unusual intervening factors.
These time estimates serve not only to determine where Judith might have been at a given moment, but also to detect unexplained deviations when compared to the established last sighting time frame.
as any route requiring significantly more or less time than reality could indicate an unexpected event.
When time markers were overlaid, mismatched route segments began to emerge, forcing investigators to consider the possibility that Judith had deviated from her habitual logical path, leading to a focus on identifying anomalous turning points.
These turning points were identified based on criteria that they offered no clear benefit in time or distance were inconsistent with the victim’s known travel purpose and often led into less monitored areas or more complex terrain.
The identification of anomalous turns was not based on subjective speculation, but on a combination of map analysis, traffic data, and knowledge of the victim’s typical travel behavior, ensuring that every assumption had a logical foundation.
From these turning points, the investigation scope was expanded to delineate high- risk zones, areas where if Judith had entered, the likelihood of an incident or external interference would be higher than in other areas.
Factors considered in delineating these zones included the degree of isolation at the time of the incident, visibility from the outside, distance from main roads, lighting conditions, and accessibility by other vehicles.
all aimed at identifying spaces that could allow a serious event to occur without immediate detection.
The delineation of high-risk zones was not intended to assert that the incident occurred there, but to establish a priority map for efficiently allocating search and investigative resources, avoiding the spread of forces over too broad and unfocused an area.
Parallel to the theoretical analysis, coordinated search operations were deployed to field check the identified high-risk areas, ensuring that assumptions about routes and risk zones were directly verified against realworld conditions rather than remaining on paper.
This coordination required collaboration among multiple teams, each assigned to sweep a specific area according to the established priority order from main routes to secondary turns and more inaccessible locations.
During the search, investigators looked not only for the victim, but also for any evidence that could confirm or rule out Judith having passed through a particular area, as even the absence of findings held value in narrowing remaining possibilities.
As areas were sequentially checked without clear results, the assumed route was continuously adjusted and updated, reflecting the investigation’s flexible yet systematic approach.
Thus, building the route was not a one-time action completed after creating an initial map, but a series of repeated analysis and verification cycles, each aimed at eliminating more implausible possibilities and focusing attention on the remaining scenarios.
The goal of this step was not to definitively state which road Judith took, but to logically identify those she could not have taken, thereby progressively narrowing the scope until only the options requiring serious consideration remained.
Through constructing feasible travel routes, estimating travel times, identifying anomalous turns, delineating high- risk zones, and conducting parallel searches.
The time gap in Judith Anne Mercer’s disappearance was transformed into a clear analytical structure, allowing her disappearance to be approached as a problem solvable through systematic investigative methods rather than scattered or emotional assumptions.
Continuing directly from the root building and possibility delineation process, the investigation’s focus had to return to the victim’s nearest point of origin, her personal circle of relationships, where individuals with frequent contact and deep knowledge of Judith Anne Mercer’s habits could provide foundational information to explain her prolonged absence.
Within this group, the closest relatives were identified as the most critical source of information to be recorded and analyzed before expanding to other relationships.
Franklin Wade Calder’s statement was formally taken in the context of him being the last person waiting for Judith’s return and the first to report her missing to the police.
Therefore, all information he provided was treated as the initial reference framework for the case file.
The recording of his statement focused not only on the specific events of the night Judith disappeared, but also on the general living context, daily schedule, communication habits, and how the two informed each other of changes in plans.
in order to determine whether Judith’s prolonged silence truly deviated from established patterns.
During this process, investigators emphasized separating objectively descriptive information from subjective assessments, as this distinction could affect interpretations of the relationship and potential motives.
The relationship between Franklin and Judith was evaluated based on multiple factors, including shared living duration, stability of family life, and any signs of tension or conflict.
But at the initial recording stage, no clear element was strong enough to conclude that the relationship was in crisis or leading to violent behavior.
However, the relationship assessment did not stop at what was directly presented, but also required cross-referencing with objective data collected during road construction, particularly time markers and gaps that could not be explained by ordinary activities.
Franklin’s statement was examined for internal consistency with each detail about time, location, and sequence of actions placed side by side to check compatibility as well as alignment with independently confirmed information from other sources.
This evaluation was not aimed at finding contradictions at all costs, but at determining the stability of the information, as consistent statements over time generally hold higher value in the early stages of investigation.
While minor discrepancies might reflect confusion or psychological stress rather than intent to conceal.
In this case, Franklin’s statement showed a certain level of consistency in the sequence of events he described.
But there were also ambiguous gaps, particularly regarding periods without independent witnesses, leading investigators to note that while no clear signs of wrongdoing existed, the file still required close monitoring.
Designating Franklin as the central subject of the file did not equate to assigning him the role of criminal suspect, but reflected the reality that he was the individual most closely connected to the victim and the primary source of many initial facts.
Therefore, all subsequent developments in the case needed to be cross-cheed against what he provided.
The central subject at this stage was understood as an information anchor point to which various hypotheses must return for consistency checks rather than a conclusion of responsibility.
Investigators maintained a cautious approach, avoiding letting focus on a single individual obscure other possibilities while simultaneously recognizing that overlooking or downplaying the role of the closest relative could create dangerous gaps in the file.
During the consistency evaluation, details about when Franklin began to worry, the communication attempts he made and his decision to contact the police were correlated with previously fixed time markers to determine whether his response was appropriate to the circumstances.
This appropriateness was measured not emotionally but by comparison with typical reactions in similar sudden disappearance cases, allowing behavior to be assessed within a broader reference framework.
Although some details could not be immediately verified, no element at this point was sufficient to establish criminal grounds or shift the file toward an accusatory direction as the most critical facts remained missing and no direct physical evidence linked Franklin to Judith’s disappearance.
Therefore, the temporary conclusion of this phase was that Franklin Wade Calder was identified as the central subject of the file based on his degree of involvement andformational value, but there was no legal basis to regard him as a criminal suspect.
This classification allowed the investigation to continue in an open manner with all new information cross-referenced against his statement and recorded context while ensuring the file was not prematurely framed into a single hypothesis.
Maintaining the status of insufficient criminal grounds also reflected the principle of investigative caution as mislabeling at this stage could lead to serious consequences from missing key clues to undermining the objectivity of the entire process.
In that context, Franklin’s role in the file was clearly but neutrally recorded, creating a necessary informationational anchor for further analysis of existing and incoming data while preserving the flexibility required to adjust investigative direction.
As the overall picture became clearer from identifying Franklin Wade Calder as the central subject of the file, but without sufficient criminal grounds, investigative activity had to return to the physical space of the case where any tangible sign could provide clues beyond the limits of statements and assumptions.
Therefore, organizing a wide area search was implemented as an inevitable step to field verify the zones delineated during route construction.
Search teams were coordinated according to the established priority areas, focusing on feasible routes, anomalous turns, and isolated high-risk spaces with the goal not only of locating the victim, but also of detecting any evidence that Judith Anne Mercer had passed through or stopped at those locations.
The search was conducted systematically with each area swept in sequence to ensure nothing was overlooked and every finding, no matter how small, was documented for cross-referencing with the constructed route map.
As the search scope gradually expanded without yielding direct results regarding Judith’s whereabouts, attention shifted to the possibility that her personal vehicle might provide more critical information since the car was directly tied to her travel route and could reflect what happened after her last confirmed appearance.
The discovery of the victim’s vehicle occurred at a location inconsistent with the previously constructed logical route, immediately making this a significant finding requiring careful handling as the location did not fall within the area.
Judith would be expected to pass through under normal circumstances.
The vehicle was found with no victim inside, and Judith’s absence from the scene immediately raised suspicion that the vehicle might have been abandoned following an unusual event rather than simply resulting from a mechanical failure or a temporary stop decision.
The discovery location was evaluated in detail geographically, including distance from main roads, degree of isolation, visibility conditions, and accessibility by others.
all to determine whether it was a reasonable place to stop under normal conditions.
Recording this anomalous location played a pivotal role as it created a new spatial anchor in the file, forcing previous route hypothesis to be re-examined and adjusted to fit the actual evidence.
Once the vehicle was confirmed as directly related to the disappearance, the decision to impound it was made to preserve evidentiary value as any disturbance at the scene could erase important signs.
Impounding the vehicle was intended not only for future forensic examination, but also to prevent external factors from altering its initial condition, ensuring all existing traces remained intact for analysis.
During this process, investigators documented the vehicle’s overall condition, including parking position, vehicle orientation, and surrounding environmental factors to create a comprehensive picture of the circumstances in which it was found.
Although the vehicle was impounded and became a key piece of evidence, the absence of the victim at the scene left a major gap in the file as this absence could not be reasonably explained by ordinary assumptions alone.
The combination of a wide area search yielding no direct results and the discovery of the vehicle in an anomalous location heightened the severity of the case as it suggested Judith had not voluntarily left the vehicle under normal circumstances.
However, at this point, investigators still avoided hasty conclusions as the vehicle discovery while a major advance did not yet provide enough information to determine exactly what happened to the victim.
The failure to locate Judith, despite expanded searches and checks of priority areas, forced the file to record that the victim remained missing, but with increasingly clear signs that this was no longer a disappearance explainable by simple causes.
The discovery of Judith Anne Mercer’s vehicle was therefore regarded as a crucial turning point in the initial investigative phase as it provided a specific spatial marker for focused analysis while raising new questions about how and why the vehicle appeared at that location without its owner.
In the context of not finding the victim, the vehicle became the sole physical lead capable of connecting hypothesis about routes, personal relationships, and various possibilities into a more structured analytical chain.
Nevertheless, Judith’s absence from the scene meant this significant discovery was still insufficient to answer the core question of the case.
It only further clarified the abnormal nature of the disappearance and confirmed that what occurred went far beyond a simple delay or misunderstanding, compelling the investigative effort to intensify based on the newly recorded evidence.
Continuing directly from the seizure of Judith Anne Mercer’s vehicle as a central piece of evidence.
Yet with the victim still missing, the investigation was forced to shift its focus to the examination of the vehicle and related crime scenes in the hope that any remaining physical traces could compensate for the absence of direct information about her whereabouts.
The vehicle was examined according to the standard procedures of the time, including documentation of its overall condition.
parking position, vehicle orientation, signs of external and internal impact, as well as environmental factors that might affect trace preservation.
The surrounding areas where the vehicle was found were also searched for any clues indicating the victim’s presence or an unusual event.
During the examination, several findings were noted as inconsistent with a normal routine scenario, including the vehicle’s location not matching the previously reconstructed reasonable route and details that led investigators to question whether the car had truly been stopped voluntarily.
However, these indicators lacked sufficient specificity to allow for a definitive conclusion.
What was documented remained at the level of anomaly, unable on its own to prove a specific criminal act or clearly establish how that anomaly occurred, expanding the examination to related sites, including areas within the priority search radius and unusual turns identified during route reconstruction, also yielded no decisive findings, as no direct traces could link a specific event to Judith’s disappearance.
Investigators noted that although many details made the case suspicious, none were strong enough to surpass the threshold of speculation and become direct probitive evidence.
In that context, the file continued to be supplemented with records of what was not found since the very absence of traces was itself a fact reflecting the case’s complexity while also highlighting the limitations of the technology and investigative methods available at the time.
Various investigative avenues were pursued in hopes of a breakthrough, from re-examining the victim’s personal relationships to checking unrelated random possibilities outside the established route.
But each encountered the same issue, a lack of sufficiently solid physical anchors to advance further.
Efforts to cross-ch checkck statements, verify timelines, and expand the search radius produced no significant change in the overall picture, as every hypothesis quickly ran intoformational gaps that could not be filled with existing facts.
During this process, investigators had to acknowledge that despite the many anomalous signs, there was no direct evidence identifying any specific individual as responsible for Judith Anne Mercer’s disappearance, and maintaining an open investigation without real progress, risk depleting resources without bringing the case closer to the truth.
The lack of direct incriminating evidence not only limited the possibility of prosecution but also affected how priorities were allocated within the investigative system as other cases with clearer facts also demanded similar attention and resources.
Investigative leads were successively considered, tested, and ultimately discarded when they yielded no concrete results, leaving behind an increasingly thick file in terms of documentation, but increasingly thin in terms of decisive evidence.
In that context, the decision about the case’s next status became a practical rather than emotional matter, as prolonging an investigation without breakthrough was not only inefficient, but could also distort expectations about the case’s solvability under current conditions.
After many years with no significant progress and when all reasonable investigative avenues had been exhausted to their limits, the file on Judith Anne Mercer’s disappearance was formally placed under cold case review, reflecting the reality that no further feasible investigative measures could be pursued at that point.
This decision did not mean the case was solved or suspicions cleared.
It merely acknowledged that the available tools and facts were insufficient to advance further.
In 1978, the file was officially designated a cold case, marking the point at which all active investigative activity ceased, and the matter was shifted to long-term archival status.
All evidence was sealed and stored per regulations, reports were finalized and systematized to ensure that should new conditions or technologies arise in the future, the file could still be fully accessed and re-examined.
Placing the file in cold case status did not close the questions surrounding Judith Anne Mercer’s disappearance.
It simply reflected the investigative limits of the time when anomalous signs had been documented but could not be transformed into evidence strong enough to establish criminal responsibility.
The cold case designation thus became the inevitable outcome of a prolonged but breakthroughless investigation in which every reasonable effort had been tested and every viable path explored, leaving an unsolved file preserved in the hope that under different circumstances and with different conditions the truth might one day be revealed.
After decades in which the file on Judith Anne Mercer’s disappearance remained archived as a cold case with incomplete notes and unexplained anomalies, an administrative decision to reopen the case was made in a completely different context from when it was sealed, reflecting fundamental changes in how long dormant cases are approached, as well as advances in modern investigative capabilities.
This decision did not stem from a newly discovered specific lead found by chance, but rather from a systematic review of cold case files in the region aimed at identifying those still possessing sufficient preserved evidence and data to warrant re-evaluation with modern methods.
During this review, the Judith Anne Mercer file emerged as a case meeting several key criteria, including the continued preservation of the vehicle, related samples, and a series of documented anomalies that had been established, but never conclusively resolved due to the limitations of the original investigative period.
The administrative order to reopen the case was issued as a formal step to reactivate the file within the current legal framework, moving it from passive storage to active investigation status and enabling the application of procedures and tools that did not exist or were not used at the time.
Alongside this decision, the entire original file was retrieved from storage and transferred to the dedicated unit for cold cases, ensuring that the reinvestigation would be conducted by a team experienced in handling long-term cases with methods suited to their unique nature.
Transferring the file to the cold case unit marked a significant organizational shift as this unit is designed to handle cases where traditional investigative methods have reached their limits, focusing on re-examining old data from fresh perspectives rather than solely seeking entirely new leads.
Upon receiving the file, the cold case unit conducted an integrity check of the documents, cross-referenced the evidence inventory with actual storage, and verified preservation conditions to ensure all necessary data for reinvestigation was available and usable without procedural disputes.
Assignment of a lead investigator occurred immediately after transfer, clearly establishing individual responsibility for the entire reinvestigation process and preventing information fragmentation or inconsistent approaches.
The assigned investigator was required to quickly master the files history from initial investigative steps and failed leads to documented but unresolved anomalies thereby forming a comprehensive view of what had and had not been done.
This assignment was not merely administrative but strategic as the lead investigator would determine priorities, methods, and scope based on balancing available resources with the goal of clarifying the case.
From the outset, one of the most critical tasks was defining the scope of the reinvestigation to avoid mechanically repeating past efforts that had already proven fruitless.
This scope was determined based on the principle of focusing on points where the original investigation had reached but could not overcome due to technological, methodological or legal limitations while excluding directions already proven unfeasible or irrelevant in the current context.
Defining the reinvestigation scope involved reviewing the preserved evidence list, assessing the potential for reanalysis of each item with modern techniques, and evaluating each fact’s relevance to new hypothesis.
At the same time, the scope was deliberately limited to prevent resource dilution, concentrating instead on elements with genuine breakthrough potential rather than uncontrolled expansion.
Throughout this process, the lead investigator had to balance respect for the original file structure with the application of fresh approaches, as any change in scope could affect the files continuity and legal reliability.
Reopening the file was therefore not seen as starting over from scratch, but as a selective continuation in which established facts retained their reference value, while past gaps and limitations became the primary targets of the new investigative effort.
The decision to reopen the Judith Anne Mercer case, the transfer to the cold case unit, assignment of a lead investigator, and definition of the reinvestigation scope formed a systematic chain of actions reflecting a clear commitment to re-examining the case in light of new conditions without distorting or denying the past record.
In this context, the file was no longer merely a set of archived documents, but became a living investigative object where every old fact could take on new meaning within a fresh analytical framework.
Reopening the file also meant accepting that past tentative conclusions might need re-evaluation but only within clearly defined boundaries, ensuring the reinvestigation remained flexible enough to accommodate new possibilities while rigorous enough to avoid baseless speculation.
Thus, part 8 concludes by establishing an organizational and methodological foundation for the new investigative phase where all subsequent actions must stem from clearly defined administrative and strategic decisions, ensuring that reopening the file is not merely symbolic, but genuinely enables a renewed effort to clarify the case under present conditions.
Continuing directly from the official reopening of the Judith Anne Mercer disappearance file and the clear definition of the reinvestigation scope, the first decisive task for this entire phase was a comprehensive inventory of all remaining evidence.
After decades in cold storage, it could not be assumed that every item collected in the past still existed fully, intact, or retained sufficient value for use in the current legal and scientific context.
The inventory process was implemented as a thorough review, beginning with cross-checking the original evidence list against actual storage records to confirm precisely what remained, what had deteriorated over time, and what might have been lost or become untraceable.
Every item retrieved from storage underwent a strict inspection procedure documenting its physical condition, preservation level, original ceiling method, and chain of custody in detail.
Since any discrepancy in these elements could diminish or eliminate the evidence usability should the case advance to deeper legal stages.
The inventory covered not only physical evidence but also the entire related documentation system from initial examination reports, scene diagrams, seizure records to investigators notes and subjective assessments from the earlier phase.
Because these documents provided essential context for understanding why an item was collected, how it was evaluated, and how it had been used in the original investigation.
After completing confirmation of the remaining evidence catalog, the next step was classification by scientific value, a process requiring careful analysis to avoid repeating past limitations while also not placing unrealistic expectations on items.
no longer capable of providing reliable information.
Evidence was evaluated against multiple criteria, potential to contain biological or physical data reanalyzable with modern technology, direct relevance to the victim or disappearance circumstances, and sufficient integrity to allow for valid conclusions.
During this process, investigators did not assume that items previously deemed unhelpful would remain so, as advances in forensic science may have opened possibilities previously inaccessible.
At the same time, some items once considered central had to be re-evaluated cautiously, as prolonged storage could have altered or degraded their original properties to the point of failing current analytical standards.
Classification by scientific value thus created a clear hierarchy, placing each item into a category reflecting its potential contribution to case resolution from those capable of generating new facts to those retaining only historical reference value.
Parallel to this classification, the controlled elimination of unavailable evidence was conducted to avoid investing time and resources in items no longer capable of yielding reliable information.
Elimination here did not mean destruction but removal from investigative and analytical priority with clear documentation of the reason for unavailability such as irreparable damage, invalid chain of custody or failure to meet technical requirements of modern analytical methods.
This approach ensured every decision could be explained and verified if necessary while maintaining a transparent and systematic file structure.
Once unavailable evidence was removed from focus, attention shifted to identifying the core evidence group, those items meeting both integrity requirements and high scientific value potential when reanalyzed in the current context.
This core group was considered the foundation of the entire reinvestigation phase, representing the rare intersection between old data and new analytical capabilities where a clear result could fundamentally alter understanding of the case.
Identifying this group was not based solely on technical assessment, but also on alignment with the previously established reinvestigation scope, ensuring subsequent efforts would concentrate on elements directly tied to core unresolved questions.
Throughout this process, investigators had to continually balance the desire to maximize exploitation of remaining data with the need to keep the investigation focused and directed as spreading resources too thinly could dilute focus and prolong the process without commensurate results.
The inventory and restructuring of evidence was therefore not merely a technical step, but a strategic decision shaping how the file would be approached throughout the reinvestigation phase.
The outcome of this step was a clear realistic picture of what truly remained in the Judith Anne Mercer disappearance file after many years of cold storage, what could be exploited with modern technology and what had to be accepted as beyond usable limits.
By eliminating unavailable elements and concentrating on the core evidence group, the file was streamlined from a large collection of scattered data into a focus structure with clear priorities, enabling all subsequent analysis to proceed on a more solid foundation.
This process also allowed the lead investigator to gain deep insight into the case’s history, not only through what was done in the past, but through the limitations that prevented resolution, thereby forming an approach that respected old facts while remaining open to new possibilities afforded by the present context.
Completing the evidence inventory marked a critical transition in the case reopening phase.
As from this point forward, the investigation was no longer guided by general assumptions or vague expectations, but driven by a deliberately selected and evaluated set of evidence, reflecting the shift from broad review to focus pursuit of elements capable of delivering genuine progress in clarifying the decades long disappearance of Judith Anne Mercer.
Continuing directly from the identification of the core evidence group following the systematic inventory and screening process, the re-examination phase is implemented as a pivotal step to transform the remaining scientific potential of the stored exhibits into analyzable, comparable, and usable data within the framework of modern investigation.
This begins with reapproaching the biological evidence that previously could not be exploited or was only examined to a very limited extent due to technological barriers.
The selected biological exhibits must simultaneously meet two fundamental requirements, sufficient physical integrity and a valid chain of custody, as any error in either factor could diminish the value of the results or render the conclusions legally untenable.
The re-examination process is designed to current standards with sample handling conducted in a strictly controlled environment to minimize cross-contamination risks while every operation is meticulously documented to ensure traceability and reverification when needed.
For biological evidence, the focus is on locating and extracting traces that can be analyzed using modern techniques, including those previously overlooked or undetectable due to insufficient sensitivity.
And this process demands patience and high precision because many samples have undergone prolonged storage over decades.
Parallel to biological re-examination, the reanalysis of geological samples is carried out to extract information on the origin and distribution of non-biological materials related to the case, an area where forensic science has made significant advances since the initial investigation.
Geological samples are analyzed not only to determine basic composition, but also to compare microscopic characteristics, allowing for a much higher degree of accuracy in assessing similarities or differences between sources compared to older methods.
The application of modern forensic technology in both biological and geological fields requires close coordination between investigators and laboratory experts as the selection of appropriate analytical methods for each sample type directly impacts the ability to obtain meaningful results.
The advanced techniques employed aim not only to maximize detection capabilities, but also to quantify the reliability of results, clearly distinguishing between statistically significant similarities and random coincidences lacking sufficient basis for inference.
Throughout this process, all initial assumptions are maintained in a neutral state as the objective of re-examination is not to confirm a pre-existing hypothesis, but to collect objective data to clarify unresolved questions in the file.
The use of modern technology also enables the processing of very small or degraded samples which was previously nearly impossible, thereby significantly expanding the scope of information obtainable from exhibits that appeared to have exhausted their value.
Throughout the re-examination, strict quality control measures are applied to ensure that final results are not influenced by technical errors or subjective factors and all analytical steps are performed in accordance with standards widely recognized in the forensic science community.
Completing the re-examination in the same year 2021 not only reflects the efficiency of the design process but also carries strategic significance for the investigation’s progress as prolonging the analysis time could disrupt the investigative flow and reduce continuity in evaluating new facts.
Completing all tests within this time frame allows the obtained results to be immediately placed in the context of the reviewed file, directly cross-referenced with old facts, and assessed holistically rather than fragmented into disjointed pieces of information.
The re-examination process is therefore not merely a purely technical step, but part of an overall investigative strategy where each result must be understood in relation to other elements of the case, from timelines and movement routes to established personal connections.
The application of modern forensic technology to old exhibits also demands a high level of caution in interpretation as highly accurate results still need to be placed in an appropriate context to avoid inferences exceeding the actual data.
In that context, completing the re-examination in 2021 marks an important milestone, shifting the investigation phase from preparation and review to one with specific scientific data for deeper analysis while affirming that the limitations that once forced the file to be shelved are no longer absolute barriers under current conditions.
The re-examination phase concludes with all core exhibits having been analyzed to the highest applicable modern standards, generating a new set of scientific results capable of changing perspectives on what occurred.
However, at this point, these results remain raw data that must be evaluated, cross-referenced, and carefully integrated into the overall picture of the case, ensuring that every subsequent step is based on a solid scientific foundation and rigorous investigative process.
Continuing directly from the completion of the entire re-examination process in 2021 and the readiness of raw scientific results for analysis within the case file context.
The investigation focus shifts to reading, understanding, and interpreting the DNA results in a manner that can withstand rigorous scientific and legal scrutiny.
This is the first time since the case occurred that biological data sufficient to support specific conclusions has emerged.
The process of identifying suspect DNA begins with comparing DNA profiles obtained from core exhibits against appropriate databases where matches are not evaluated simplistically as positive or negative but must be placed within a framework of probabilistic analysis and contextual contact.
When a DNA profile shows a match exceeding the accepted statistical threshold, the data is considered of investigative significance but not sufficient on its own to establish liability as the presence of an individual’s DNA in a given context always requires explanation by reasonable possibilities.
The subsequent focus is therefore on analyzing contact locations, that is determining where on the exhibit the DNA was found, under what circumstances, and in what manner its presence could be explained.
Contact location analysis plays a pivotal role as the same DNA profile can carry entirely different meanings depending on the location and context of discovery, directly affecting the probative value of the result.
Forensic experts and investigators collaborate to assess whether the contact location aligns with ordinary daily interactions or whether it is in areas where the DNA presence can only be explained by an unusual event.
In this process, every hypothesis about how the DNA could have been transferred is considered from direct and indirect contact to secondary transfer possibilities, ensuring no reasonable possibility is overlooked before concluding on the results significance.
Evaluating the probative value of DNA relies not only on the degree of match, but also on the ability to exclude harmless scenarios.
As DNA, despite its high accuracy, remains just one piece in the overall picture, if not placed in relation to other case facts, investigators must consider whether the DNA result can independently explain existing gaps in the case or merely reinforces existing assumptions without generating new information.
In this context, excluding random contact becomes a mandatory requirement as any match can be questioned if the DNA presence cannot be proven to be non-incidental or through legal and harmless interactions.
This exclusion is achieved by cross-referencing DNA results with the history of relationships between involved individuals, recorded habits, and possible contact contexts under normal conditions.
to determine whether a reasonable explanation exists for the DNA presence beyond a scenario directly related to the case.
When random contact possibilities are considered and successively excluded based on specific facts, the probative value of the DNA result is elevated to a new level, shifting from a scientific indicator to a factor capable of playing a central role in the investigative argument.
However, even at this stage, caution is maintained as investigators are fully aware that over interpretation or isolating DNA from the overall context can lead to erroneous conclusions, weakening the entire file if challenged.
Therefore, DNA results are analyzed in parallel with previously established facts, including movement routes, vehicle discovery locations, and key timelines to assess compatibility between biological data and the overall case picture.
This compatibility is not measured subjectively, but by checking whether the DNA result explains recorded anomalies and reasonably narrows remaining possibilities.
When these factors are juxtaposed, the DNA result begins to demonstrate the potential to provide an answer the file has lacked for decades while simultaneously raising higher requirements for crossverification and quality control as any error at this stage could have serious legal consequences.
Standardized result reports are prepared accompanied by probabilistic analysis and detailed methodological explanations ensuring that every conclusion can be understood and evaluated by parties not directly involved in the examination process.
This serves not only internal investigative purposes, but also prepares for the possibility that DNA results will be used in future legal proceedings where every detail may be scrutinized.
During evaluation, investigators continually question the limits of the data, recognizing that DNA, no matter how powerful, is not infallible evidence if not placed correctly within the evidentiary structure.
The balance between maximizing the scientific value of DNA results and maintaining a cautious approach has made this phase a substantive but unhurried advancement.
By the time the analysis is complete, the DNA results are no longer raw data, but have been transformed into a clearly investigative element with its probative value determined within the scope of what it can and cannot establish.
This phase concludes with investigators holding a crucial piece strong enough to reshape perspectives on the case, but still requiring careful integration into the overall file, ensuring every next step is based on a full understanding of both the strength and limitations of the DNA results in clarifying the prolonged disappearance of Judith Anne Mercer.
Continuing directly from the analysis, interpretation, and proper placement of DNA results within the overall evidentiary structure, the investigation focus shifts to the geological data group as an independent verification direction to assess the consistency of the scientific conclusions, beginning with comparing mud samples collected from the scene related to Judith Anne Mercer’s vehicle with mud samples preserved from various locations in the file.
Scene mud samples are processed according to modern forensic procedures with each sample separated into microscopic components to identify characteristic geological features including grain structure, mineral composition, organic ratios and environmental indicators reflecting formation conditions.
This analysis does not aim for general similarity, but focuses on rare isas capable of distinguishing between different mud sources within the same geographic area as only these have reliable value in linking or excluding locations.
After completing the analysis of seen mud samples, investigators proceed to compare them with mud samples collected from the suspect’s residence.
A step requiring high caution as every conclusion must be based on scientific similarity rather than speculation based on geographic distance or personal relationships.
Residents mud samples are processed in parallel with scene samples using the same procedures and standards to ensure all comparisons occur on the same technical basis, avoiding discrepancies due to differing methods.
During comparison, experts focus on matching each microscopic characteristic, determining the degree of match, and assessing the probability of those characteristics appearing simultaneously at unrelated locations, as only when this probability is sufficiently low can a conclusion of linkage have scientific value.
Geological origin conclusions are not based on a single factor, but result from synthesizing multiple indicators, each contributing to strengthening or weakening the similarity hypothesis between samples.
When these indicators show a high degree of similarity, exceeding the threshold explainable by random coincidence, experts conclude that the mud samples have indistinguishable geological origins by current methods.
a conclusion with significant investigative implications.
This conclusion does not absolutely affirm that the mud samples come from a single unique point, but excludes the possibility of them originating from clearly distinct geological environments, thereby significantly narrowing the range of reasonable scenarios.
Linking the suspect to the location through soil data is achieved by placing the geological conclusion within the overall case context where vehicle discovery location, feasible movement routes, and previously established timelines serve as the reference framework.
Investigators assess whether the presence of mud with similar origins at both the scene and suspect’s residence aligns with ordinary daily activities or requires specific contact with that geological environment within the time frame consistent with the case.
In this process, harmless explanatory possibilities are seriously considered, including incidental mud transfer or through unrelated activities to ensure conclusions are not inflated beyond actual data.
When these possibilities are cross-referenced with specific case facts and fail to provide a reasonable explanation for the degree and location of mud presence, the linkage value of geological evidence is significantly elevated.
However, investigators maintain necessary caution recognizing that soil like DNA does not exist in a vacuum and always requires interpretation in relation to other factors.
Therefore, soil comparison results are placed alongside DNA results, not to replace, but to cross-check, determining whether these two independent evidence streams lead to compatible conclusions.
Compatibility between these results is considered a key factor in evaluating the solidity of the investigative argument.
As when multiple different evidence sources point in the same direction, the likelihood of reflecting truth is higher than relying on a single data type.
Linking the suspect to the location through soil evidence is not presented as a final conclusion, but as an additional piece that clarifies how the physical elements of the case may have intersected during the period of Judith Anne Mercer’s disappearance.
In synthesis, standardized geological reports are prepared and interpreted in clear language to ensure conclusions can be understood and evaluated by non-experts in the field.
an important requirement if results are to be used in subsequent legal steps.
Investigators also emphasize documenting the limits of geological analysis, acknowledging that while results show high similarity, science does not permit absolute identification of a single unique source and this transparency strengthens the overall reliability of the evidence.
Upon completion of the entire comparison and interpretation process, the soil results become a key component in the evidentiary structure, providing a physical bridge between the suspect and the location related to the case that had not previously been scientifically established.
This phase concludes with investigators possessing a second independent evidence stream independent of biological data yet showing considerable consistency with prior findings thereby reinforcing the scientific foundation of the file and necessitating serious consideration of the connection between the suspect and key locations in the decadesl long disappearance of Judith Anne Mercer.
Continuing directly from the establishment, evaluation, and crossverification of independent scientific evidence lines, including DNA results and soil analysis with a high level of reliability.
The investigation moves into the most comprehensive synthesis phase to date, reconstructing the sequence of events.
The goal is to connect all old and new data into a logical sequence capable of consistently explaining the prolonged disappearance of Judith Anne Mercer.
This work is not approached as retelling a story, but as a complex investigative puzzle where each piece of evidence must be placed in the correct position in space and time while remaining compatible with every other established fact.
Investigators begin by systematizing all prior evidence from the initial investigation phase, including the last confirmed sighting of the victim, possible travel routes, the location where the vehicle was found, and any previously noted anomalies that could not be explained at the time.
They then place these facts alongside the new forensic results to reassess their significance from a modern perspective.
The integration of old and new evidence does not proceed linearly, but through multiple rounds of analysis, each aimed at testing whether new information alters the understanding of old facts, and conversely, whether old facts impose limits or require adjustments to the interpretation of new results.
From this foundation, investigators reconstruct the sequence of events chronologically, starting from the moment Judith was last confirmed to be seen in normal activity, followed by the period of lost contact, unaccounted time gaps, and finally the discovery of her vehicle in an anomalous location.
Each point in this sequence is tied to specific facts, avoiding unsubstantiated assumptions to ensure the reconstructed timeline accurately reflects what has been proven rather than what is speculated.
Throughout the reconstruction, investigators pay particular attention to temporal plausibility, as this factor most objectively eliminates or reinforces scenarios.
Every hypothesized action in the sequence must satisfy physical constraints, including travel times between locations, the feasibility of actions within the allowed time frame, and consistency with previously fixed milestones.
Scenarios requiring unrealistic amounts of time or conflicting with established milestones are discarded immediately, regardless of how narratively compelling they may appear.
Alongside temporal plausibility checks, the sequence is also evaluated for behavioral plausibility, whether the hypothesized actions align with the known habits, relationships, and psychological context of the involved individuals.
This helps avoid constructing a sequence that is physically correct but lacks human credibility, a common pitfall in investigations relying solely on technical data.
Once a preliminary sequence is constructed, investigators cross-check each link against independent evidence streams, especially DNA and soil, to determine whether the sequence can explain the presence and context of these traces.
A sequence is retained only if it can simultaneously account for the location and context of DNA findings, the degree and location of soil deposits, and the position and condition of the vehicle when discovered.
Sequences that explain only part of the evidence or require additional unproven assumptions are deemed insufficiently robust to serve as the foundation for the main hypothesis.
This process is highly iterative.
Each time a hypothesis is discarded or modified, the entire sequence must be re-examined to ensure that connections between milestones remain intact.
Through multiple rounds of analysis, the range of plausible scenarios gradually narrows from many initial possibilities to a very small number of sequences that do not contradict known facts.
A complete hypothesis emerges when one sequence stands out as the only plausible explanation that consistently accounts for all evidence lines without relying on baseless additional assumptions.
This hypothesis is not constructed to make the story complete, but is designed as a working model in which every element has a clear role and can be independently tested.
Investigators actively seek out weaknesses in the hypothesis, pose counter scenarios, and check whether any alternative explanation can achieve a comparable level of consistency.
Only when the main hypothesis withstands these challenges does it become strong enough to serve as the basis for subsequent investigative steps.
The reconstruction also involves clearly identifying critical junctures in the sequence points where a small change in timing or location could collapse the entire structure to help investigators understand which elements must be most rigorously protected and verified.
Throughout this process, all conclusions are recorded with their corresponding level of certainty, clearly distinguishing between proven elements and those still reliant on reasonable assumptions to avoid prematurely turning a hypothesis into a conclusion without sufficient legal basis.
The sequence reconstruction phase does not aim to close the case, but to create a sufficiently rigorous explanatory framework to guide focus subsequent investigative actions, avoiding unnecessary expansion or revisiting directions already proven infeasible.
By the end of this section, investigators possess a complete hypothesis about what may have happened to Judith Anne Mercer during the period of her disappearance.
A hypothesis built on a tight integration of old and new evidence.
Rigorously tested for temporal and behavioral plausibility and robust enough to serve as the foundation for the next decisive steps in the investigation while maintaining the necessary caution to allow adjustment if new facts emerge.
Continuing directly from the formation of a complete hypothesis regarding the sequence of events built on a tight integration of old and new evidence, the investigation shifts to the phase of direct confrontation with the most relevant individual in the file.
The reinterview of Franklin Wade Calder.
The aim is to test the explanatory capacity of his personal account against a reconstructed event structure that is far more detailed and logically rigorous than at the time of the initial investigation.
The rein is prepared meticulously, not only procedurally but also strategically as investigators recognize that this is not a routine questioning but a comprehensive test of the consistency of his account over time.
In a context where many objective facts have altered the understanding of the case, Franklin is invited to participate as a key person of interest and the interview is designed to allow him to present again everything he believes happened from the events on the day Judith Anne Mercer disappeared to his own reactions and actions in the subsequent period.
Throughout this process, investigators avoid imposing conclusions or making direct accusations.
Instead, focusing on fully documenting his account to enable detailed comparison with prior statements in the file.
The comparison of old and new statements is conducted systematically.
Each time point, action detail, and subjective observation is placed side by side to assess stability or change across decades.
Changes in statements can reflect various possibilities from memory fade to deliberate adjustments to fit a new context.
Investigators pay particular attention to details Franklin emphasized in the past, checking whether they are still maintained with the same level of certainty and whether the current account introduces previously unmentioned elements.
During the comparison, several discrepancies begin to emerge, not as immediate blatant contradictions, but as subtle shifts in sequence, timing, or level of detail, requiring careful analysis to determine whether they result from memory degradation, or indicate systemic inconsistency.
Identifying material contradictions does not rely on minor differences, but focuses on points where the new account no longer aligns with fixed time milestones or objective facts established through scientific analysis.
When a detail in the account requires an infeasible time period or directly conflicts with the vehicle’s discovery location or other physical evidence, it is flagged as a material contradiction requiring clarification.
Investigators do not rush to conclusions, but continue probing the account to see whether Franklin can provide a reasonable explanation for these contradictions, as the ability to explain is itself an important indicator of reliability.
During the rein, numerous unusual details are noted, not in the form of confessions or extreme reactions, but as silences, changes in response patterns, and attempts to avoid questions directly related to key points in the reconstructed sequence.
Investigators observe that when asked about general aspects, Franklin’s account flows smoothly and consistently, but when addressing specific time points or situations tied to new evidence, the level of detail and certainty drops marketkedly.
These unusual details are recorded objectively without assigning meaning beyond what can be proven.
Yet, they are not dismissed as they appear precisely at points where the investigative hypothesis suggests pivotal events may have occurred.
The rein is not intended to force Franklin to admit a specific scenario, but to test whether his account can coexist with the reconstructed sequence without generating unresolvable contradictions.
As the interview progresses, investigators note that maintaining a consistent narrative becomes increasingly difficult for Franklin when confronted with tight time constraints and unadjustable physical facts.
Once identified, material contradictions are documented along with an analysis of their severity and potential impact on the overall reliability of the account, distinguishing between tolerable deviations and points that significantly undermine credibility.
The entire rein process is meticulously documented to ensure that all assessments are based on specific data rather than subjective impressions from investigators.
a critical requirement in decadesl long cases where memory and context can become distorted over time.
At the conclusion of the reinterview phase, investigators do not draw immediate conclusions, but proceed to integrate the new account with all existing evidence, evaluating whether the recorded contradictions and unusual details are sufficient to alter the status of the file.
This section closes with Franklin Wade Calder’s account having been subjected to an unprecedented level of scrutiny in the case’s history, not only compared to his own prior statements, but also against a scientifically grounded, temporally rigorous event structure.
The outcome of the rein is not treated as a final resolution but as a crucial test of the investigative hypothesis where the compatibility or incompatibility of the personal account with the overall picture becomes a pivotal factor in assessing the credibility of the reconstructed sequence while also providing the necessary data to make the next decisions in handling the case.
Continuing directly from the reinterview of Franklin Wade Calder in which material contradictions and unusual details were systematically recorded, the investigation shifts to the file consolidation phase.
The objective is to conduct an overall evaluation of all collected evidence to determine whether the current evidentiary structure is sufficiently robust to meet the necessary legal threshold.
This phase does not focus on seeking new evidence, but on reviewing, organizing, and reassessing what already exists, as the file can only withstand rigorous judicial scrutiny if the existing pieces are linked logically and consistently, investigators begin by reviewing all evidence by previously identified categories from biological data and geological results to fix time milestones and old and new statements from involved individuals to ensure no element is overlooked or misassed in the overall picture.
The holistic evidence evaluation follows the principle of not prioritizing any single evidence stream but assessing each element’s value in relation to others.
As the true strength of the file lies not in individual pieces, but in the convergence of multiple independent lines pointing to the same reasonable conclusion.
During this process, investigators pose the core question, “Does each piece of evidence consistently contribute to explaining the reconstructed sequence of events? And are there any internal contradictions between evidence streams that could undermine the overall argument? Logical coherence is tested as a stress test on the entire file with every assumption and intermediate conclusion cross-ch checked against actual facts to ensure they do not rely on inferences beyond what the evidence permits.
Investigators pay particular attention to intersection points between scientific evidence and witness statements as these are the locations where inconsistencies, if present, will be most apparent.
When scientific results indicate a specific possibility, related statements must be able to coexist with that possibility without temporal spatial or behavioral conflicts.
Otherwise, the mismatch is recorded as a factor increasing suspicion.
During the logical review, alternative scenarios previously considered in the sequence reconstruction phase are re-examined against the current evidence set to determine whether any other scenario can explain the facts with comparable plausibility.
The absence of an equally compelling alternative scenario is seen as a strong indicator that the main hypothesis enjoys clear logical and evidentiary advantage.
Once the evidentiary structure has been tested and demonstrates internal consistency, the next step is to assess whether the file has reached the threshold for establishing probable cause, a legal standard requiring a lower level of proof than conviction, but sufficient to believe a crime has occurred and that a specific individual is reasonably connected to it.
Establishing probable cause does not rely on subjective impressions, but on whether a reasonable person presented with the same set of evidence could conclude that the suspect may have been involved in the investigated events.
Investigators analyze each element in the file from this perspective.
The presence of DNA at a contact location inexplicable by random interaction.
geological similarities linking the suspect to the relevant site and material contradictions in the account that cannot be reasonably explained within the fixed time frame.
When these elements are considered collectively, they form a logical chain of inference that surpasses mere suspicion, allowing the conclusion that probable cause has been established on solid grounds.
However, reaching this threshold does not mean the file is ready for every legal scenario as the next phase requires careful preparation to ensure the entire prosectorial file can withstand challenges from the defense.
Therefore, prosecutorial file preparation proceeds in parallel with probable cause establishment, focusing on arranging evidence in a clear logical sequence, clarifying the connection between each element and the overall sequence of events and eliminating unnecessary details that could dilute the focus.
Scientific reports are standardized in language to ensure technical conclusions are presented accurately yet accessibly to non-experts.
An important requirement if the file is presented to prosecutors and later to a jury.
Statements and interview transcripts are reviewed to ensure material contradictions are clearly documented along with analysis of their significance in the overall context, preventing critical details from being buried in a large volume of information.
During prosecutotorial preparation, investigators also proactively consider potential weaknesses, placing themselves in the defense’s position to anticipate possible attacks on the evidence and thereby refining presentation and adding necessary explanations to minimize risk.
This approach is not about embellishing the file but ensuring every conclusion is supported by clear reasoning and specific facts ready for adversarial legal scrutiny.
The consolidation phase is thus not merely a technical completion, but a shift in mindset from pure investigation to prosecutorial preparation where evidentiary standards become stricter and every inference must be presented transparently.
By the end of this section, the file on Judith Anne Mercer’s disappearance has been consolidated into a tightly constructed structure with evidence lines logically linked, probable cause established on reasonable grounds, and the entire documentation prepared for handover to the appropriate authorities for consideration of next steps, marking the case’s transition beyond the pure investigative phase into a new threshold where legal accountab capability can be pursued based on a meticulously and systematically built evidentiary foundation.
Continuing directly from the point where the case file has been systematically strengthened, the lines of evidence logically linked, and the threshold of probable cause established.
The next decisive step is to present the entire case file to the grand jury to seek approval for the necessary prosecutorial actions as required by law.
This is a process that demands thorough preparation as it marks the first time the case is presented to an independent authority tasked with evaluating the reasonleness of the accusatory arguments.
The case file is presented in a standardized structure beginning with the context of the disappearance, the initial investigative steps, the period when the case was frozen and the reopening process.
then focusing on the new scientific examination results, the reconstruction of the sequence of events, and the critical inconsistencies in Franklin Wade Calder’s statements.
This provides the grand jury with a complete but concise picture without unnecessary excess.
The presentation is not aimed at persuading through emotion, but at demonstrating that the existing evidence, when viewed as a whole, is sufficient to believe that a crime occurred and that the suspect is reasonably connected to it, meeting the legal standard to proceed with arrest and prosecution.
Investigators work closely with prosecutors to ensure that every conclusion is supported by specific data, scientific reports are clearly interpreted, and any potentially contentious points are explained within a framework of caution, avoiding exaggeration or speculation beyond the evidence.
After the grand jury reviews the case file and concludes that the necessary standards have been met, an official arrest warrant is issued, marking the transition from the investigative phase to the law enforcement phase with the goal of bringing the suspect into the judicial process.
The issuance of the arrest warrant follows proper procedure, including determining the scope, conditions, and appropriate timing to minimize risk and ensure safety for all involved parties.
Given that the suspect has lived freely in the community for decades and the arrest must be conducted in a controlled manner, the arrest plan is developed based on an assessment of the suspect’s routine, surrounding environment, and security factors, ensuring the action is swift, effective, and free of unforeseen situations.
Once the timing is determined, law enforcement proceeds to approach the suspect according to the plan, clearly informing him of the arrest warrant and his rights under the law, ensuring all procedures are transparent and properly followed.
The arrest of Franklin Wade Calder occurs in a controlled manner with no signs of resistance or significant security incidents reflecting the cautious and thoroughly prepared approach of law enforcement in a highly sensitive case spanning decades.
Immediately after the arrest, the suspect is transferred to complete booking procedures as required, including identity verification, recording of initial condition, and ensuring access to necessary legal services, a critical step to safeguard the legality of the entire prosecutorial process.
Completing the booking procedures is not merely administrative.
It also marks the suspect’s official entry into the phase of judicial oversight where all subsequent actions are recorded and closely monitored.
Throughout this process, investigators maintain focus on preserving the integrity of the case file, avoiding any actions or statements that could compromise objectivity or create legal risks in later stages.
The arrest is not viewed as the end of the investigative effort, but as the inevitable outcome of a prolonged evidence accumulation process where every step was carefully weighed to ensure the final decision rests on a solid foundation.
Once booking is complete, the case moves into a new phase, shifting focus from determining possible involvement to preparing for trial within the formal legal framework.
This phase concludes with Franklin Wade Calder having been lawfully arrested, marking the first time since 1974 that an individual has been placed in a position of direct criminal accountability for the disappearance of Judith Anne Mercer while also reflecting the transformation of the case from a decadesl long cold case into an actively prosecuted matter in the modern justice system.
Continuing directly from Franklin Wade Calder’s lawful arrest and completion of booking procedures, the focus of the case officially shifts from the investigative phase to the prosecutorial phase where the entire case file is transferred to the prosecution for evaluation under a stricter legal lens with the objective of clearly defining the appropriate charges and the feasibility of bringing the case to trial.
The assigned prosecutors do not start from scratch, but approach a carefully prepared evidentiary structure, including the full initial investigation, the period when the case was frozen, the reopening process, modern scientific examination results, the reconstruction of the sequence of events, and the critical inconsistencies in the suspect’s statements.
The case file is received according to standard procedure with prosecutors reviewing each part to ensure all evidence was legally obtained, properly preserved, and capable of withstanding defense challenges as any procedural error could undermine the entire case regardless of the strength of the substantive evidence.
The prosecution’s initial focus is on identifying the most appropriate charges based on the existing evidence.
a strategic decision that not only affects the potential penalty range, but also shapes the entire argumentative direction at trial.
Determining charges requires weighing the nature of the alleged conduct, the elements of the crime under current law, and the ability to prove each element with specific evidence, particularly in a case from decades ago with no living victim to provide direct testimony.
Prosecutors must assess whether the current evidence is sufficient to prove each element of the charges beyond a reasonable doubt or whether a different charge better reflects the achievable level of proof.
Concurrently, prosecutors begin developing the trial strategy with the goal not only of presenting the evidence fully, but also of arranging it in a logical understandable sequence for the jury who may lack expertise in forensics or criminal investigation.
This strategy includes identifying which evidence will serve as pillars which will be supportive and which points may become targets for defense attacks thereby preparing rebuttal arguments to protect the legality and probative value of the case file.
During this process, prosecutors work closely with investigators and forensic experts to ensure all scientific conclusions are accurately interpreted, avoiding oversimplification or misleading language, as clarity and consistency in presentation are key to maintaining credibility in court.
Trial preparation also includes anticipating defense arguments, particularly challenges related to the passage of time, the reliability of evidence after many years, and possible innocent explanations for scientific traces, allowing prosecutors to build approaches to counter each potential line of attack.
Once the strategic elements are set, the critical procedural step with significant legal weight is filing the indictment in which the prosecutors formally present the charges against Franklin Wade Calder based on the selected offenses and supporting evidence.
Filing the indictment marks the point at which the suspect is no longer merely detained for investigation, but officially becomes a defendant in a criminal case with corresponding procedural rights and obligations.
The indictment is drafted carefully to accurately reflect what the prosecution can and intends to prove at trial, avoiding unsubstantiated or overreaching allegations, as any discrepancy could be exploited to weaken the case.
In filing the indictment, prosecutors ensure that every element of the charges is clearly presented with references to specific evidence showing the logical connection between the alleged conduct and the collected data.
This serves not only legal purposes but also defines the scope of the trial as what is stated in the indictment becomes the framework limiting subsequent arguments and evidence.
Once the indictment is filed and accepted, the case officially enters the pre-trial phase where all subsequent activities revolve around preparing for a public trial and the focus shifts from whether there is sufficient basis to charge to whether that basis is sufficient to persuade a jury beyond a reasonable doubt.
Thus, the prosecution phase is not merely a procedural step following arrest, but a fundamental transformation of the entire process from investigation to adversarial litigation where every piece of evidence and argument must be presented and defended in a rigorous legal environment.
As this phase concludes, the Judith Anne Mercer case has crossed the boundary between investigation and prosecution with Franklin Wade Calder now formally facing the criminal charges outlined in the indictment and the entire investigative file now on the trajectory of trial where the truth will be tested not only by investigative logic but by the highest standards of proof in the justice system.
Continuing directly from the filing of the indictment and Franklin Wade Calder’s formal status as a defendant before the judicial system, the trial opens as the pivotal phase where the decadesl long investigation must undergo the most rigorous scrutiny in an adversarial courtroom setting.
From the very first days of trial, emphasis is placed on presenting the core evidence in a tightly structured manner to help the jury understand not only each individual piece of evidence, but also how they connect to form a cohesive overall picture.
Prosecutors do not approach the trial as a dry technical recitation, but construct the presentation logic based on chronology and causal relationships.
Starting with Judith Anne Mercer’s disappearance, the period when the case was frozen, and especially the scientific discoveries made after the case was reopened, key evidence is introduced in sequence to build a foundation of understanding for the jury with forensic data presented first due to its objective nature serving as the pillar for the entire accusatory argument.
In the forensic science portion, prosecutors sequentially present DNA and soil mud analysis results, not merely stating conclusions, but allowing experts to explain the methods, quality control processes, and scientific limitations, ensuring the jury not only hears the results, but understands how they were obtained.
Experts clarify that extracting and analyzing DNA from old evidence requires stricter protocols than usual and adherence to these standards ensures the results are highly reliable under current conditions.
The defense quickly seizes on the complexity of forensic science to counterattack, raising questions about possible contamination, sample degradation over time, and interpretation based on probability rather than absolute certainty.
These questions force experts to delve deeper into explaining that forensic science does not provide absolute certainty but offers a sufficiently high probability to support reasonable conclusions and that the methods used have been validated and widely applied in similar cases.
The forensic debate becomes intense as both sides repeatedly contrast their interpretations of the results.
one emphasizing the cumulative probative value, the other highlighting limitations and the possibility of doubt.
After the forensic evidence is presented and thoroughly debated, prosecutors shift focus to the timeline, treating it as the skeletal framework connecting all evidence.
The timeline is presented step by step beginning with the last confirmed sighting of Judith Anne Mercer, unexplainable time gaps, the location where the vehicle was found, and relevant physical trace milestones.
Prosecutors emphasize that this timeline is not a single assumption, but the result of systematically eliminating implausible scenarios based on time and space constraints.
The defense counters by pointing out remaining uncertainties in the timeline, arguing that the inability to pinpoint every minute creates room for alternative scenarios and that the prosecution is asking the jury to accept a sequence of events based on inference rather than direct evidence.
The timeline debate becomes one of the longest portions of the trial as it is where both sides repeatedly clash over the standard of reasonleness in connecting events and the jury must weigh whether the remaining gaps are large enough to sustain reasonable doubt.
In parallel, prosecutors present the analysis of Franklin Wade Calder’s inconsistent statements as a reinforcing factor, not to prove he lied in every minor detail, but to show that his statements cannot consistently coexist with established objective facts.
Key inconsistencies are presented by directly comparing old and new statements against fixed timelines, highlighting explanations that require impossible conditions in terms of time or space.
The defense responds by arguing that human memory degrades over time, especially in a decades old case, and that inconsistencies in statements cannot be taken as proof of criminal conduct.
This debate forces the jury to consider the extent to which they are willing to accept changes in statements as a natural phenomenon and at what point such changes seriously undermine credibility.
Throughout the trial, the way each side presents evidence reveals two entirely different strategies.
Prosecutors repeatedly return to the big picture, emphasizing the convergence of multiple independent lines of evidence while the defense attempts to isolate each line from the broader context to diminish their combined weight.
The debates over forensics timeline and statement inconsistencies do not stand alone, but interweave continuously, creating a complex argumentative structure where each side’s strengths become the others targets.
The trial is therefore not merely a forum for presenting truth as the prosecution argues or for defending reasonable doubt as the defense seeks, but a space where two interpretations of the same set of facts are placed side by side for the jury to evaluate.
The judge ensures the proceedings remain within legal bounds, limiting excessive speculation while allowing each side to fully present its arguments, thereby protecting the fairness of the trial.
By the time closing arguments conclude, the jury has received a vast amount of information from complex technical details to extended logical arguments.
and their task is not just to recall each piece of evidence, but to understand how they connect or fail to connect as each side contends.
The trial closes the examination and argument phase in an atmosphere of tension where the central question is no longer whether Franklin Wade Calder was involved, but whether the totality of the presented evidence is sufficient to persuade beyond a reasonable doubt under the highest standards of the justice system.
This phase marks the culmination of the entire prosectorial process where years of investigation, analysis, and argumentation are placed before the final judgment of those not involved in the process.
And as this phase ends, the full responsibility for determining the defendant’s legal fate passes to the jury in a state of serious deliberation based on what has been publicly and adversarially presented in court.
Continuing directly from the climactic phase of the trial where the prosecution presented its entire structure of evidence and chain of accusatory arguments to the jury, the defense officially launches its counter strategy with the goal not of reconstructing a complete alternative narrative, but of weakening each pillar in the prosecution’s case, thereby restoring and maintaining reasonable doubt about the defendant Franklin Wade Calder’s criminal responsibility for the disappearance of Judith Anne Mercer.
The overall defense strategy is built on the principle that in a case spanning decades with no direct eyewitnesses and no body discovered during the initial investigation, every conclusion must be subjected to especially rigorous scrutiny and any gaps or assumptions can serve as the foundation for reasonable doubt.
Rather than outright denying the entire case, the defense chooses a segmented approach, attacking each group of evidence individually to diminish the cumulative strength the prosecution seeks to build.
The first focus of the counter strategy is challenging the value of the DNA evidence, which the prosecution regards as the strongest scientific proof in the case.
The defense emphasizes that DNA, while highly accurate, does not exist outside of context, and the discovery of the defendant’s DNA on items related to the victim, does not automatically equate to criminal conduct, especially given the marital relationship between the two, which involved frequent and lawful contact in the past.
Defense attorneys question the possibility of DNA transfer in circumstances unrelated to any crime, including prior direct contact, indirect contact, or secondary transfer through intermediaries, thereby arguing that the presence of DNA, regardless of location, still requires explanation within a broader context rather than being treated as self-inccriminating evidence on its own.
At the same time, the defense exploits the long-term storage of the physical evidence, raising concerns about sample degradation, the risk of crosscontamination during decades of preservation, and the inevitable limitations of applying modern technology to old samples, all to sow doubt about the absolute reliability of the results.
These arguments do not seek to completely reject forensic science, but to highlight that such science always comes with probabilities and limitations, and that any conclusions based on DNA must be weighed carefully in a case lacking other direct evidence.
After focusing on DNA, the defense shifts to challenging the soil sediment evidence, the geological line of proof the prosecution uses to link the defendant to locations related to the case.
The strategy here is to emphasize the non-uniqueness of soil within the same broad geographic area, arguing that similar geological characteristics can appear at multiple locations, especially in regions with relatively uniform geological conditions.
Defense attorneys focus on the scientific language in the reports, pointing out that a conclusion of indistinguishable geologically does not equate to identifying a single unique source and that interpreting this as a direct link risks inflating the probative value of the evidence.
In this way, the defense seeks to downgrade the role of the soil evidence from a strong linking piece to a merely supportive factor that cannot stand alone without other more independent and direct evidence.
Alongside challenging each line of scientific evidence, the defense also focuses on proposing alternative hypotheses to demonstrate that the sequence of events constructed by the prosecution is not the only reasonable explanation for what occurred.
These hypotheses do not need to be proven true, only sufficiently plausible to maintain doubt based on gaps in time, space, and information in the record.
The defense stresses that Judith Anne Mercer’s disappearance occurred within a time frame where many factors cannot be fully verified and that the failure to locate the victim in the early years of the investigation opens the door to scenarios other than the accusatory hypothesis.
These scenarios are presented as logical possibilities, not based on emotional speculation, but on the very uncertainties the prosecution itself acknowledges, such as unresolvable time gaps or the absence of direct evidence of criminal conduct at a specific location.
By this method, the defense shifts the focus from the question, “Does the evidence exist?” to does this evidence completely rule out every other reasonable possibility in line with the criminal standard of proof.
Throughout its counter strategy, the defense avoids offering a detailed alternative story that could easily be rebutted by the prosecution.
Instead, maintaining an open approach that continually emphasizes the prosecution’s burden of proof and that any flaw in the accusatory argument must be interpreted in the defendant’s favor.
The attorneys also exploit the case’s long duration to argue that human memory, paper records, and social context can all distort over time, making reconstruction of events after decades less certain than in contemporaneous cases.
The ultimate goal of the defense phase is not to prove Franklin Wade Calder’s absolute innocence, but to persuade the jury that the prosecution’s carefully constructed case still falls short of the certainty required to overcome reasonable doubt.
When the defense presentation concludes, the picture of the case before the jury is no longer the single line structure the prosecution desired, but a multi-dimensional argumentative space where each piece of evidence carries unanswered questions.
This part closes with the scales of justice tip toward greater balance, forcing the jury to confront their most difficult task directly, determining whether the doubts raised by the defense are reasonable enough to preclude a guilty verdict based on everything presented openly at trial.
Continuing directly from the defense phase where the prosecution’s entire argumentative structure was subjected to systematic challenge, the trial process moves into the decisive yet highly cautious stage of overall legal evaluation.
A phase that is no longer a confrontation between the two sides, but a comprehensive weighing to determine whether the current record meets the strictest legal standards of criminal procedure.
The first focus of this stage is assessing the admissibility of the evidence.
That is examining whether all evidence presented in court was collected, preserved, analyzed, and presented in compliance with the legal requirements in force at the respective historical times.
In a decadesl long case like that of Judith Anne Mercer, this requirement becomes especially complex because legal and technical standards have evolved over time, forcing the justice system to evaluate evidence not only against current norms but also against the norms valid at the time of collection.
factors such as the chain of custody, continuity of records, authority of the examining agencies, and adherence to procedures at the time of the initial investigation are all carefully scrutinized to ensure no serious violations exist that would render the evidence legally inadmissible.
for scientific evidence reanalyzed during the reopening of the case.
The focus is on the transparency of modern procedures, the possibility of independent retesting, and compliance with widely accepted scientific standards.
As only when these elements are assured can the results be accepted as legally valid evidence in court.
After determining that the core evidence is not excluded on procedural grounds, the evaluation shifts to its persuasive strength.
a more synthetic aspect that relies less on rigid rules than on admissibility.
At this stage, the question is no longer is the evidence admissible, but does this evidence truly help clarify the truth and more importantly whether when considered together they form a sufficiently strong argumentative system to lead to a single reasonable conclusion.
The assessment of persuasive strength does not occur evidence by evidence but holistically where the value of each element is considered in relation to the others because in criminal trials the strength of a case often lies in the convergence of multiple independent lines of evidence pointing in the same direction.
The DNA results in soil analysis are weighed not only for their individual scientific meaning but also for how they support the timeline and contradictions in testimony.
thereby forming a structure of inference with internal coherence.
However, it is precisely here that the issue of reasonable doubt emerges as the central axis of the legal evaluation because the standard for conviction does not require absolute certainty, but requires the exclusion of every reasonable doubt about the possibility of the defendant’s innocence.
The doubts raised by the defense are examined systematically, not dismissed simply because they disadvantage the prosecution, but placed in the overall context to determine whether they arise from genuine weaknesses in the record or are merely theoretical possibilities unsupported by specific facts.
This consideration is especially difficult in long cold cases where the absence of certain direct evidence is unavoidable and the justice system must decide whether those absences are sufficient to maintain reasonable doubt when faced with a consistent but circumstantial body of evidence.
Doubts concerning the possibility of incidental DNA contact, the non-uniqueness of soil or the degradation of memory over time, are placed alongside fixed facts to assess whether they break the logical chain between pieces of evidence or merely highlight the inherent limitations of any prolonged investigation.
In synthesizing the arguments of both sides, the justice system does not seek to reconcile opposing views, but to determine whether the prosecution has met its burden of proof.
The prosecution’s case is evaluated based on its ability to present a seamless chain of inference, where each intermediate conclusion is supported by evidence and not based on unfounded assumptions.
while the defense’s arguments are evaluated based on their ability to identify points where that chain of inference can be interrupted by reasonable doubt.
This process is not a simple balancing of the two sides, but a rigorous examination to determine whether after considering all counterarguments, a reasonable path of inference leading to conviction still exists.
The legal evaluation also includes examining the role of the jury.
Those who did not participate in the investigation and are not influenced by the case’s long history, yet must render a verdict based solely on what was presented at trial.
This places the requirement that the evidence and arguments be not only legally and scientifically correct, but also clear enough for ordinary people to understand and apply the reasonable doubt standard fairly.
The legal evaluation phase thus becomes the convergence point of all previously presented elements where forensic science, timeline, logic, human testimony, and legal standards intersect in a complex weighing process.
When this part concludes, the case does not move closer emotionally or dramatically, but it reaches full legal maturity where all necessary elements for a final decision have been placed on the scales fully and cautiously.
This is the stage where the justice system pauses to reflect, not to seek additional facts, but to determine whether what exists is sufficient to cross the fragile boundary between reasonable doubt and the legal certainty required for a verdict, preparing for the conclusive step of the entire trial process.
Continuing directly from the legal evaluation phase where all evidence, arguments, and reasonable doubts have been carefully weighed, the trial process enters the most pivotal moment, the deliberation by the court and jury, a procedurally closed phase, but one carrying decisive weight for the entire decad’s long case.
During deliberation, the jurors review what was presented at trial, not based on emotion or fleeting impressions, but on the specific legal instructions regarding the standard of proof, especially the principle of reasonable doubt to determine whether the prosecution’s case meets this threshold.
Deliberation is not a simple vote, but a deep discussion process where each line of evidence is revisited.
Each contradiction in testimony is weighed and each defense counterargument is placed alongside established scientific facts and timeline logic.
The jurors must confront the core question whether the convergence of DNA evidence, soil analysis, timeline, and key contradictions in testimony is strong enough to lead to a single reasonable conclusion or whether a reasonable alternative scenario remains that has not been fully excluded.
Throughout this process, the court ensures that deliberation occurs within the legal framework, free from extraneous influences and strictly adhering to instructions on applying the law to proven facts.
When deliberation concludes and the jurors reach the required unonymity, the next step is establishing criminal responsibility, a decision not merely based on whether the defendant was involved, but on whether the alleged conduct has been proven beyond reasonable doubt according to the elements of the offenses charged in the indictment.
Establishing criminal responsibility reflects the outcome of the entire weighing process where accusatory and defensive arguments have been placed in overall context and evaluated not as disjointed pieces but as a complete structure.
Once criminal responsibility is established, the trial moves to the sentencing phase where the official verdict is publicly announced, marking the first time since Judith Anne Mercer’s disappearance that the justice system issues a clear legal conclusion regarding responsibility for the case.
The sentencing is conducted in proper order with the court clearly stating the verdict based on the established offenses while noting that the decision was reached after full consideration of the evidence, arguments, and applicable legal standards.
The pronouncement of the verdict is not merely a procedural moment, but the convergence point of the entire investigation and trial process where years of effort by law enforcement, prosecutors, and the justice system crystallize into a legally binding conclusion.
After the verdict is announced, subsequent legal procedures are completed to ensure the court’s decision is properly enforced, including recording the judgment, determining statutory appeal rights, and finalizing procedures related to the defendant’s custody or management according to the pronounced verdict.
This post-verdict phase also includes ensuring that all procedural rights of the parties are respected from the defendant’s right to appeal to the state’s obligation to enforce the sentence lawfully and transparently.
The court’s verdict not only closes a specific trial, but also marks the case’s official transition out of the contentious phase into the post-trial stage, where the legal consequences of the decision begin to take effect.
For the justice system, this is the moment of affirming that the standards of proof have been applied seriously and that the final decision reflects a careful balance between protecting society and safeguarding individual rights under the law.
When this part concludes, the verdict has been pronounced, criminal responsibility established, and all necessary legal procedures completed, placing an official marker on the end of the prolonged trial process while transferring the case to a new phase where the verdict’s impact will extend beyond the courtroom into broader legal and social life.
Continuing directly from the pronounced verdict and the completion of post-trial legal procedures, the case officially enters the closure phase with the file recorded as a cold case solved, marking the procedural end of a decad’s long journey where every investigative step, every review and every final scientific effort converge to bring the case out of its historical deadlock.
The case status update is carried out under strict administrative procedures.
transferring the file from the list of unresolved matters to the list of cleared cases accompanied by all legal documents confirming the final verdict and the enforcement of the sentence in accordance with regulations.
This process is not merely formal, but reflects the justice systems official recognition that all key questions regarding criminal responsibility have been answered within the framework of the law and that no further investigative requirements remain related to the same chain of events.
The final archiving of the file is conducted with a high degree of care as it is not merely an administrative document but a historical record reflecting the evolution of investigative methods and forensic science across generations.
All physical evidence, analysis reports, interrogation transcripts, trial documents, and court decisions are systematized and archived according to current standards, ensuring future accessibility for research, review, or legal reference while protecting data integrity against loss or distortion.
During this phase, the relevant agencies confirm that no further investigation will be expanded as all reasonable investigative avenues were fully pursued during the reopening and no legal or factual basis exists for continuing to examine other individuals or scenarios.
The decision not to expand the investigation does not stem from fatigue or a desire for quick closure, but from an assessment that all reasonable doubts were considered during the trial and resolved within the framework of the final verdict.
Case closure also includes updating information in internal management systems to ensure all relevant units share the same understanding of the files current legal status avoiding unnecessary duplication or reactivation of investigative activities in the future.
For investigators who participated in various stages of the case, this is a moment of responsibility handover where the file no longer belongs to any specific individual or unit but becomes part of the shared archive reflecting the final outcome of collective efforts spanning many years.
Recording the case as cold case solved does not erase the irreversible limitations and losses caused by time, but it establishes a clear boundary between prolonged uncertainty and a legally concluded status, allowing the justice system to close a file without leaving unanswered questions within its scope of responsibility.
During closure, the authorities also review the procedures applied in the case, not to change the conclusion, but to record lessons learned about evidence preservation, approaches to long-term cases, and the role of modern technology in breaking historical deadlocks, treating this as a reference for similar future cases.
The final file is archived not merely as a resolved case, but as evidence of the justice systems ability to revisit past errors or limitations and apply modern tools to achieve results within the bounds of the law.
When the case status update is fully completed, all procedural obligations arising from the case are confirmed as fully fulfilled.
from notifying the parties involved to ensuring appeal rights have been exercised within statutory deadlines.
The closure phase does not generate additional drama or new developments, but it carries decisive meaning by placing an official full stop on a file that had hung in limbo in the system for decades.
When this part ends, the Judith Anne Mercer case no longer exists as an open question in unresolved investigative categories, but is recorded as a clarified case with a clear legal status and the file permanently archived per regulations.
The decision not to expand the investigation further affirms that all necessary steps were taken and that the justice system within the limits of law and evidence has reached its final conclusion.
The case closure phase therefore does not aim to create an emotional sense of ending but to establish legal and administrative completion where the file is responsibly transparently and based on the entire process closed allowing the case to leave the present investigative realm and enter judicial history as a solved cold case.
In the United States today, the story of Judith Anne Mercer shows that a missing person should never be treated as a private matter or something that will resolve itself.
The starting point of the case, Judith leaving her last confirmed location, not arriving as scheduled, unreachable.
family waiting then forced to call the police is a very everyday scenario that many American families still encounter especially in the context of personal vehicle travel and packed schedules.
The first lesson is to treat normal markers such as punctuality, communication habits and expected destinations as critical safety signals when they break.
Acting early makes a difference.
The second lesson lies in the fact that a case file closed in 1978 did not mean the truth disappeared.
It demonstrates the importance of data retention and small traces.
Soil samples and biological evidence were once powerless in the 1970s.
But when the cold case unit reopened the file in 2021, DNA and soil conclusions created independent links, forcing investigators to reconstruct the timeline.
Reinterview Franklin Wade Calder and uncover critical contradictions.
Therefore, in real life, keep baseline information, planned routes, license plates, check-in habits, emergency contacts, and don’t hesitate to update family members on any plan changes.
Those small details can become life-saving timelines.
Finally, the trial shows that science is powerful, but does not speak for itself.
How you recount events, consistency, and the ability to provide reasonable explanations in light of objective facts all matter.
In American culture, the practical lesson is prepare in advance safety plan, act early, report early, and view transparent cooperation with law enforcement as part of community responsibility, not an inconvenience.
If you find the decadesl long journey to solve the Judith Anne Mercer case offers profound insight into justice and the power of forensic science, please subscribe to the channel so you don’t miss other cold case stories gradually being revealed.
Thank you for following until the very end and see you in the next video where we will continue together to reach the ultimate truth.
News
Family Vanished from Stillwater Lake Texas in 1995 — 27 Years Later FBI Found Box with Clothes
In the summer of 1995, the Whitlock family vanished without a trace during their weekend retreat at Stillwater Lake. Their…
SOLVED: Pennsylvania Cold Case | Samuel Foster, 10 | Missing Boy Found Alive After 54 Years
54 years ago in a peaceful town in Pennsylvania, 10-year-old Samuel Foster vanished without a trace after an ordinary afternoon,…
SOLVED: Illinois Cold Case | Sandra Wallace, 3 |Missing Girl Found Alive After 18 Years(2003 – 2021)
18 years ago, in a peaceful suburb in Illinois, a three-year-old girl vanished from her home in just a few…
SOLVED: Florida Cold Case | William Rodriguez, 6 | Missing Boy Found Alive After 50 Years
In 2022, a belated miracle tore through the thick dust of 50 years of despair. A six-year-old boy who vanished…
Just One Year After She Vanished and the Search Ended — Her Body Was Found Floating in a Lake
The last confirmed sighting of the 22-year-old came from a gas station security camera just after midnight. The footage was…
THREE TEENAGERS WENT MISSING ON PROM NIGHT IN 1973 24 YEARS LATER, ONE DISCOVERY REVEALS A SHOCKING TRUTH
In 1973, three teenagers left their prom after what was supposed to be just an ordinary end to their high…
End of content
No more pages to load