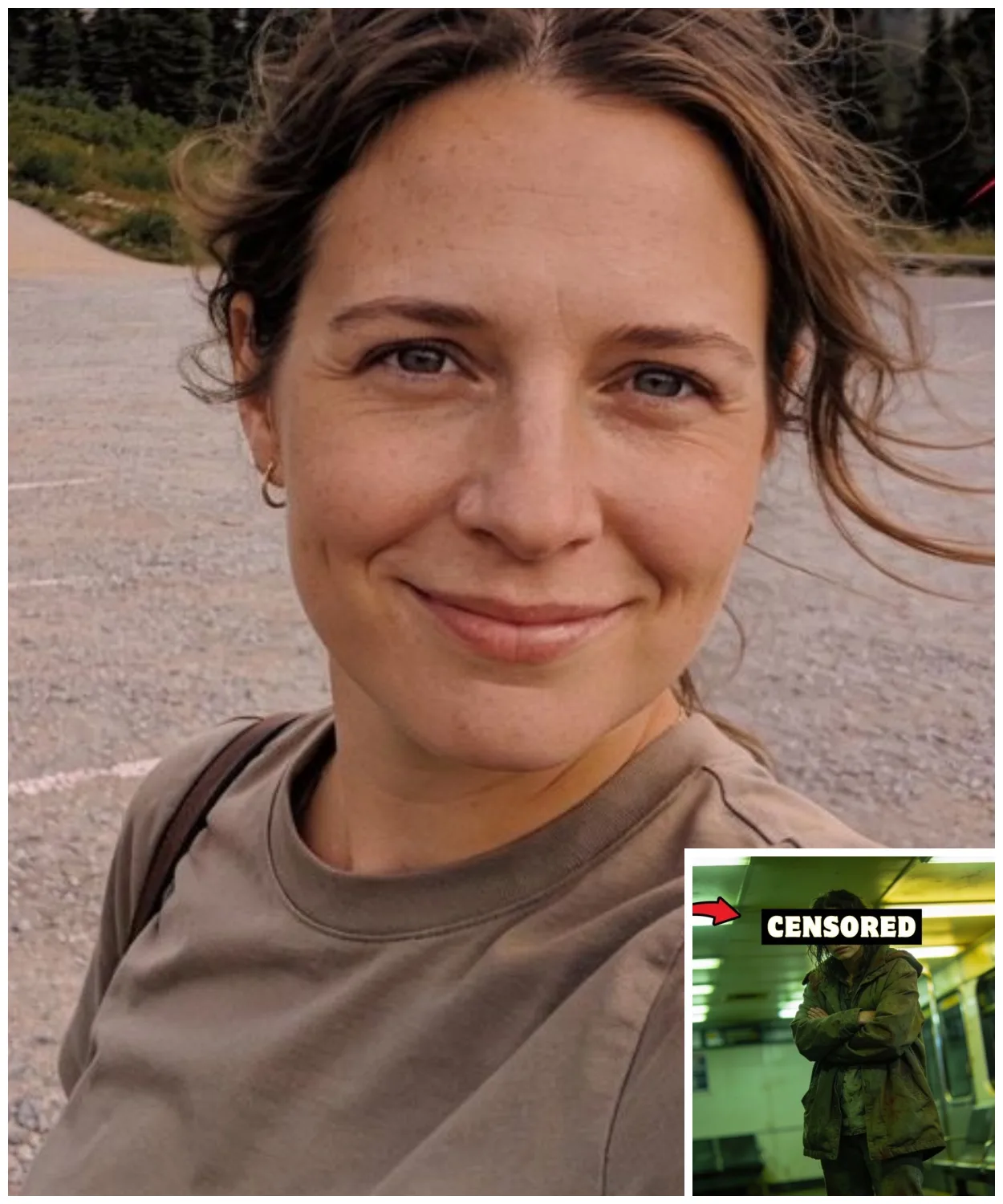
When Felicia Lewis appeared at the Yakama bus station on a cold fall morning, she was almost unrecognizable, gaunt to the point where her coat swallowed her up, hair matted and greasy, hands trembling from sheer exhaustion.
The woman who had gone missing 14 months earlier near Mount Reineer, presumed dead or permanently vanished, now stepped out of the shadows on her own with no luggage, no identification, and no explanation whatsoever.
But what stopped the police cold wasn’t her physical condition.
It was the moment Felicia lifted her head and spoke a name.
In that instant, everyone understood that the story behind her disappearance wasn’t an accident, but something far more dangerous.
Some names and details have been changed to protect identities and privacy.
Before we dive into the story, don’t forget to subscribe to the channel and hit the notification bell so you don’t miss the latest cases.
On a morning in late June, the public parking lot on the western edge of Mount Reineer National Park carried the familiar calm of peak tourist season when Felicia Lewis turned off her engine and stepped out of the car.
Felicia, 34 years old, was a single mother living in Tacoma, Washington.
She worked part-time in the service industry and raised her young daughter in a modest apartment in a suburban neighborhood.
She had no criminal record, no involvement in legal disputes, no outstanding debts, and no ties to any complicated social groups.
Her life revolved around work, her daughter’s school, and steady daily routines.
That day trip, according to what Felicia told her family before leaving home, wasn’t a long vacation or an adventurous journey.
It was just a short drive up to the park’s edge to breathe some fresh air and step away from weeks of built-up stress.
She left in the early afternoon, taking main highways that were busy and flowing smoothly with no weather advisories in effect.
On the surface, this trip looked no different from hundreds of other quick visits by local day trippers.
The area where Felicia parked was an asphalt lot near the entrance to a short trail considered a transitional zone between public space and the park’s natural edge.
People came and went steadily, but the spot wasn’t tightly monitored by cameras or fixed ranger checkpoints.
According to witnesses present at the time, Felicia was dressed casually and carried no specialized hiking gear or large backpack, indicating she had no intention of venturing deep into the woods.
The weather was cool, cloudy, but dry with good visibility and a moderate number of visitors, enough to give a solo person a reasonable sense of safety.
A couple later told police they saw Felicia standing by her car, having a brief conversation with an unfamiliar man.
He wasn’t wearing a park uniform, carried no obvious tourist equipment, and showed no signs of aggression.
The interaction lasted only a few minutes with no tense gestures, and Felicia displayed neither anxiety nor hurry, so the moment drew no special attention amid the flow of people.
After that brief exchange, there were no further confirmed sightings of Felicia at the parking lot or nearby areas, and her vehicle was not observed leaving the location, according to statements from others present in the following hours.
The afternoon passed without any reported unusual activity, until night fell, and Felicia failed to return to her Tacoma apartment as planned.
Her cell phone went unanswered, and no texts or calls came in to explain any change of plans.
Her family initially assumed she was just running late.
But as the hours stretched through the night with no response to repeated attempts to reach her, worry quickly turned to panic.
By the end of the night, when her complete loss of contact could no longer be explained by ordinary reasons.
Relatives had no choice but to contact authorities to report her missing.
This closed the final confirmed chain of events of that day and marked the moment when Felicia Lewis, a woman with a clear schedule and a stable life, vanished without a trace.
Right that very night when Felicia Lewis failed to return to her residence and all attempts to contact her failed, the Pierce County Sheriff’s Office officially accepted the missing person report and opened a case file under standard procedure for an adult with no history of running away or high-risisk behavior.
Initial investigators noted that Felicia had a stable routine, clear family responsibilities, and showed no signs of preparing to leave her everyday life.
Based on the last confirmed information from family and witnesses, authorities quickly identified the primary focus area as the western edge of Mount Reineer National Park, where Felicia was last seen.
And within just a few hours, local police coordinated with National Park Service rangers to launch the initial search operation.
Because Mount Reineer is a vast area with complex terrain, this collaboration was considered an essential step to leverage knowledge of the landscape, trail systems, potential hazard zones, and historical accident data.
The next morning, once daylight conditions allowed, the search expanded with multiple units involved.
Ground search teams made up of police officers, rangers, and trained volunteers.
K-9 units brought in to track sent at the parking lot and main access points and helicopters deployed for aerial sweeps of dense forest areas, steep slopes, and hard-to-reach ravines.
In the early phase, the search was tightly contained around the parking lot where Felicia had stopped, the nearby short trails, popular visitor rest spots, and any secondary roads that could lead out of the park.
Since the initial hypothesis centered on the possibility that Felicia had gotten lost, suffered an accident, or experienced a medical emergency while traveling alone.
Weather conditions during those first few days were relatively favorable.
no heavy rain or thick fog, so ground teams could push farther into fringe forest areas without major obstacles, while helicopters maintained regular grid pattern flights to spot any unusual signs on the terrain surface.
However, despite highintensity efforts carried out over several consecutive days, the results yielded no decisive discoveries, no body, no clear evidence of a fatal accident, and none of the typical indicators seen in prolonged missing in the wilderness cases such as scattered clothing, dropped personal items, or improvised distress signals.
The K9 teams, even after being brought back multiple times to the parking lot and main trails for rechecks, were unable to establish any consistent scent trail leading deeper into the woods, which increasingly undermined the theory that Felicia had walked off into the wilderness.
In parallel with the field search, Pierce County Police reviewed surrounding traffic routes and checked traffic cameras on the main highways leading into and out of the area.
During this phase, however, the collected data showed no clear footage of Felicia’s vehicle leaving the vicinity after the last confirmed witness sighting.
A key detail investigators noted was that throughout the entire initial search, not a single personal item belonging to Felicia was recovered at the scene.
From purse, cell phone, shoes to any small everyday objects that commonly turn up in accident or lost in the woods scenarios.
The complete absence of these traces created a significant gap in reconstructing what might have happened.
As days passed without new progress, the search perimeter had to be gradually expanded to include surrounding areas of Mount Reineer, such as roads leading out of the park and popular tourist stopoff points.
But even with the wider scope, the outcome remained unchanged.
For Felicia’s family, this period was an agonizing stretch of waiting filled with fragile hope.
For law enforcement, it was the point when initial theories began to be seriously challenged by the total lack of physical evidence.
When the first week of searching ended without any breakthrough discovery, participating units were forced to reassess the effectiveness of direct search operations and acknowledge a troubling reality.
Felicia Lewis had vanished from a busy public area without leaving any sign of death or any tangible clue behind.
And the initial search phase, despite being conducted according to protocol and with substantial resources, had failed to answer the most basic question about her fate.
After the initial searches concluded without yielding any decisive findings, the Pierce County Sheriff’s Office proceeded to compile all the data collected from the scene, witness statements, traffic surveillance reviews, and reports from the National Park Service, rangers at Mount Reineer National Park with the goal of systematically reassessing what had and had not been established in the disappearance of Felicia Lewis.
The internal summary showed that despite high-level resources having been mobilized over many consecutive days, there was still no single piece of physical evidence strong enough to steer the investigation in a clearer direction, no body, no accident traces, no personal belongings, no continuous scent trail, and no camera footage confirming either Felicia’s departure from the area or any mishap after the last confirmed witness sighting.
On that basis, investigators sequentially evaluated the standard official hypotheses commonly applied in wilderness area missing person cases.
First was the possibility of an accident, including a fall, slipping down a slope, or sudden medical emergency.
But this hypothesis steadily lost weight as the expanded search failed to uncover any disturbed terrain, clothing, or items that could be linked to a serious incident.
The theory of becoming lost in the woods was also examined closely, especially given Mount Reineer’s history of documented cases in which visitors underestimated the terrain and natural conditions.
However, in Felicia’s case, the fact that she carried no hiking gear, had no plan to venture deep into the back country, and left behind absolutely no trace of movement along any trail made this possibility increasingly unconvincing over time.
A third hypothesis, voluntary departure, was raised as a procedural possibility to cover all scenarios.
Yet, when cross-checked against Felicia’s personal background, investigators noted there were no signs whatsoever of preparation to sever ties with her current life, whether in finances, employment, family responsibilities, or personal relationships.
The fact that she vanished completely without taking any essential items also did not align with the typical pattern of deliberate voluntary departures.
Nevertheless, because no physical evidence or direct witness testimony existed to indicate third-party involvement, authorities were unable at this stage to establish a criminal element, a critical legal threshold that determines whether an investigation will be maintained at full scale or scaled back.
In internal evaluation memos, the case was described as lacking sufficient data to upgrade to a criminal investigation, which meant there was not enough basis to issue a broader alert, form a dedicated task force, or request federal assistance at that time.
Based on these assessments, Felicia Lewis’s file was officially reclassified within the police management system as a missing person case with cold case status, a procedural change that carried major implications for the pace and priority level of the investigation.
This reclassification meant that active search operations, including wide area patrols, mobilization of volunteers, and aerial support, would cease, giving way to a passive monitoring mode in which new information would only be reviewed if received from external sources or if unusual developments arose.
For Felicia’s family, this decision was communicated as an unavoidable reality after many weeks without progress.
For the investigative file itself, it marked the moment the case moved out of emergency status and entered long-term archival storage.
Documents, search maps, witness reports, and technical data were organized, sealed, and placed into the county’s archival system with a note that the matter could be revisited if new information emerged in the future.
Local media, which had followed the case closely in the early days, gradually shifted attention to other stories.
The name Felicia Lewis appeared less and less frequently in news reports, mostly only as brief mentions in lists of still unlocated missing persons.
Administratively, the case was never fully closed, but in practical terms, it entered a state of dormcancy, where every hypothesis continued to exist side by side, yet none was strong enough to receive priority, and the prolonged absence of evidence turned time itself into the only element that kept moving forward.
By the time the file was formally archived, Felicia Lewis was no longer considered an active missing person case.
She had become a name on a roster of unresolved matters, a cold case that starkly reflected the limits of search efforts when confronted with complete traceless disappearance of an individual from a vast public space.
14 months after Felicia Lewis’s missing person file was transferred into the archival system on what seemed like an ordinary early fall morning at the central bus station in Yakima, the arrival of a woman in a state of extreme exhaustion disrupted the familiar rhythm of the place in a way no one could have predicted.
The woman stepped off a long-d distanceance bus with no significant luggage, her clothes hanging loosely on an emaciated frame, shoulders slumped as if bearing an invisible weight, skin grayish and parched, clear signs of prolonged malnutrition rather than temporary fatigue.
Her gate was unsteady, steps slow and cautious, eyes constantly scanning the surroundings with heightened alertness, as though every movement in the public space demanded intense focus.
Bus station staff noticed her not because of disruptive or panicked behavior, but due to her unusual silence and obviously unstable physical condition, prompting them to approach and check on her.
Instead of immediately seeking social services or medical help, the woman requested contact with local police, a choice that steered the situation toward official handling from the very start.
When Yaka police arrived, the woman showed no negative reaction, no evasion, and no confusion about her identity.
She voluntarily stated her full name and date of birth, information that matched a missing person file that had remained dormant in the system for over a year.
The moment the name Felicia Lewis appeared in the initial intake report created a distinct break in routine procedure because the self- return of a long-term missing person is a rare occurrence that always requires a high level of verification.
Felicia was taken to a secure and private work area within the police station where officers noted that despite her weakened state, she maintained a reasonable degree of mental clarity, understood the questions asked, and grasped the purpose of the identity verification.
She carried no obvious identification documents, but the basic personal details she provided from her previous residence address to small specifics about her family circumstances demonstrated a level of consistency that would be extremely difficult to fabricate or achieve in a case of mistaken or false identity.
During the intake process, officers observed multiple signs indicating that Felicia’s condition did not align with the voluntary departure hypothesis.
Severe weight loss, signs of dehydration, old healed injuries on her skin, and a startled reflex when approached from behind elements typically associated with prolonged stress rather than a voluntary trip.
As initial verification procedures were carried out, the state database quickly returned a match between the information Felicia provided and the previously established missing person file, reinforcing the conclusion that the woman sitting before the officers was indeed Felicia Lewis, the person who had vanished from her everyday life 14 months earlier at the edge of Mount Reineer.
In the intake reports, Yakima police recorded that Felicia did not immediately request contact with her family.
did not inquire about the legal status of her file and did not voluntarily offer any explanation for the time that had passed, an attitude that forced officers to adjust their approach toward caution, avoiding additional pressure in the early phase.
When asked about her journey to Yaka, Felicia confirmed only that she had used public transportation and traveled on her own, but provided no details about her point of origin, transfer points, or individuals she may have encountered during the process, creating a significant information gap right from the first minutes of her reappearance.
Given her concerning physical condition, Felicia was transferred to a nearby medical facility for preliminary evaluation per protocol while police completed the remaining identity verification steps and notified relevant agencies that a long-term missing person had voluntarily returned.
In the medical environment, initial observations continued to support the assessment that Felicia’s condition was not the result of a short-term incident, as the signs of debilitation indicated a prolonged period of neglect inconsistent with ordinary accident scenarios or free wandering.
At the same time, Felicia’s selectively cooperative demeanor, willing to provide necessary information for identity confirmation while deflecting any questions that could lead to reconstructing events during her disappearance, was documented as a key factor to be considered in the overall evaluation.
For law enforcement, Felicia’s reappearance under these circumstances fundamentally altered the perception of the case because an adult returning on her own after more than a year missing, in a state of severe physical decline, and with a high degree of information control, could not be easily explained by the administrative hypothesis used when the file was reclassified as a cold case.
Preliminary findings recorded in internal reports emphasized that Felicia’s physical condition, behavior, and manner of return did not fit the model of voluntary departure.
Nor did they align with prolonged wilderness disorientation or unreported accident scenarios, thereby raising the possibility that throughout those 14 months, Felicia had been in a situation controlled by external factors.
Although at this intake stage, no official conclusions or charges had yet been issued, Felicia Lewis’s self-reappearance from missing status was sufficient to shatter the administrative silence surrounding the case, compelling authorities to treat the matter as far more serious than previously assessed and laying the foundation for a new phase of evaluation, one in which Felicia’s existence was no longer in question, but the time she was missing had become the central unresolved mystery.
Right after Felicia Lewis was admitted to the local medical facility in Yakima and her condition was stabilized to the minimum level that allowed administrative procedures to proceed, law enforcement began implementing the full identity confirmation protocol designed specifically for long-term missing persons who voluntarily return.
A process built to completely rule out any possibility of mistaken identity, impersonation, or file discrepancies.
First, Felicia’s fingerprints were taken and directly compared against the Washington State Biometric database, which holds records from her driver’s license and previous administrative procedures.
The results showed a perfect match, further solidifying the evidence that the woman receiving care was indeed Felicia Lewis, the person who had disappeared 14 months earlier.
In parallel with the fingerprint comparison, Felicia’s prior medical records were retrieved, including previous examinations, medical history, basic biological markers, and personally recorded physical characteristics stored in the health care system, all of which aligned with her current condition according to the medical team’s assessment, from blood type to other relatively unchanging physical traits.
Additional administrative data such as residency records, insurance information, employment history, and documents related to her child were also reviewed to ensure there were no overlaps or contradictions between the identity.
Felicia reported and the archived information and the outcome of this process continued to confirm a high degree of consistency.
Once technical identity verification was fully completed, Yakima police immediately notified the Pierce County Sheriff’s Office, the agency that originally handled the missing person file, and updated the case status in the statewide inter agency management system, a step with significant legal weight because it formally moved the case from archive status back to active.
Notifications were also sent to the agencies that had participated in the initial search, including National Park Service Rangers, to ensure all relevant units were aware of the latest development and prepared to coordinate if needed.
Felicia’s family was contacted through official channels, not with a routine phone call, but with the support of a victim advocate officer to prepare them psychologically for the news that Felicia had been located alive, but in severely debilitated condition.
Their reaction was recorded as a mix of joy and shock, and per law enforcement recommendation, an in-person meeting was not arranged immediately to avoid adding further psychological stress to Felicia during this sensitive phase.
Based on the initial assessments of Felicia’s physical and psychological state, authorities decided to place her under special protective status, a measure commonly applied in cases where criminal involvement is possible, but not yet clearly established.
This decision included restricting public disclosure of her treatment location, controlling the list of individuals permitted to have contact with her, and implementing basic security measures to ensure she could not be approached unlawfully in the early stages of her return.
Felicia was given a brief and straightforward explanation of these protective measures presented in a non-coercive manner, and she consented without objection.
A detail officers noted as an indication that she understood the seriousness of the situation.
Alongside victim protection, law enforcement also implemented information control measures, particularly as local media began circulating rumors about a long-term missing person having returned.
Per management directive, no detailed press release was issued at this time, and all external information requests were answered with only minimal confirmations, limited strictly to acknowledging that a missing person had been safely located.
Restricting media contact was deemed necessary, not only to safeguard Felicia’s privacy, but also to prevent distortion or unnecessary complication of the ongoing initial evaluation, which was taking place amid a complete lack of information about what had happened during the 14 months, she was absent.
Internally within law enforcement, preliminary evaluation reports were compiled to synthesize all new data arising from Felicia’s reappearance, including her physical condition, behavior, level of cooperation, and elements inconsistent with the prior administrative hypothesis.
And these very reports laid the groundwork for a critical decision, reopening the investigation at an entirely different level than the original search phase.
No longer regarded as a disappearance of unknown cause, Felicia Lewis’s case was reclassified internally as one showing signs of external interference, even though the specific nature had not yet been determined.
This allowed investigators access to greater resources and more in-depth investigative procedures.
The reopening of the file did not occur publicly or with fanfare.
It was handled through administrative updates, priority adjustments within the system, and reassignment of responsible officers, reflecting the standard way law enforcement agencies manage sensitive cases when information remains limited.
For Felicia, the phase of identity confirmation and placement under special protection unfolded in an atmosphere that was both urgent and cautious with every step carefully weighed to avoid causing further harm.
For law enforcement, this was the moment when a case once considered closed began to reopen.
Not because of a specific clue or detailed statement, but because of the living presence of the victim herself, a factor powerful enough to transform the entire approach and demand a complete re-examination of every assumption that had previously led to classifying the file as a cold case.
After Felicia Lewis’s identity was confirmed and she was placed under the necessary protective measures, she was transferred to a specialized medical facility for a comprehensive health evaluation, not only to treat acute issues, but also to determine the long-term impacts her body had endured throughout the 14 months she was missing.
The medical process was carried out in layers, beginning with a general physical examination, measurement of vital signs, and an overall assessment of debilitation, then expanding to paracclinical tests aimed at reconstructing the physiological picture of Felicia during the long period without medical oversight.
Initial results showed she was in a state of severe malnutrition with a body mass index significantly lower than what had been recorded in her pre-disappearance medical file, reflecting a prolonged energy deficit rather than weight loss due to acute illness or deliberate dieting.
Blood tests revealed deficiencies in multiple essential micronutrients, including iron, protein, and key vitamins critical for neurological and immune function, along with electrolyte imbalances commonly seen in individuals forced to sustain life under unstable and insufficient dietary conditions.
Muscularkeeletal function assessment indicated pronounced muscle atrophy particularly in large muscle groups along with reduced endurance and mobility.
Evidence that Felicia’s body had undergone a long phase of adaptation to low energy levels and continuous physical stress.
Doctors noted that this pattern of emaciation was inconsistent with a short period of neglect and typically appears only when nutritional needs and rest are controlled or restricted over an extended time.
Beyond nutritional markers, the examination also documented widespread signs of overall physical exhaustion, including chronic fatigue, sleep disturbances, and exaggerated physiological responses to ordinary stimuli, reflecting a prolonged state of nervous system stress.
On the body’s surface, doctors observed healed or partially healed injuries at various locations distributed unevenly and not corresponding to a single accident, suggesting these impacts had occurred in repeated episodes over a prolonged period.
During deeper evaluations related to reproductive and endocrine health, the medical team recorded abnormal signs indicating that Felicia’s body had been subjected to involuntary and repeated interventions.
Though specific details were documented with extreme care and discretion to avoid causing additional psychological trauma to the victim.
These manifestations combined with old infections and prolonged physiological imbalance formed a medical pattern commonly documented in individuals placed in circumstances of long-term physical and personal control rather than in cases of accident or personal choice.
Equally important, the medical team systematically ruled out alternative scenarios that could explain Felicia’s condition, including the possibility of a severe accident, followed by unassisted survival, untreated chronic illness, or voluntary abandonment of her previous life to live in deprivation.
Imaging studies and organ function assessments showed no evidence of a single life-threatening injury that went untreated, nor any underlying disease that could account for such profound debilitation in a relatively short time frame.
The fact that Felicia had no hospital admission or medical treatment records during her entire time missing, combined with her reappearance without any medications or medical support devices, further undermined the hypothesis that she had voluntarily lived in free roaming deprivation.
The doctors concluded that the combination of prolonged malnutrition, physical exhaustion, repeated injuries, and abnormal signs related to bodily autonomy formed a consistent medical pattern with cases of long-term captivity and exploitation where the victim had no control over living conditions, nutrition, or personal health care.
The comprehensive medical report emphasized that these findings not only reflected past injuries, but also demonstrated that Felicia’s body had undergone a forced adaptation process in which physiological functions were pushed to their limits to sustain life in an unsafe and deprived environment.
On the basis of these conclusions, the possibility that Felicia voluntarily left to live under such conditions was ruled out to a high degree, as there was no personal motive, psychological history, or social circumstance suggesting she would choose or accept a situation that caused such severe and prolonged damage to her physical health and reproductive capacity.
For law enforcement, the medical file became the first objective foundation providing scientific support for the hypothesis that Felicia’s disappearance was not the result of a random chain of events, but was likely connected to some form of organized control and exploitation.
Although the medical team avoided conclusions beyond their professional scope, the language used in the report with terms such as systematic deprivation and signs of repeated intervention was sufficient to draw a clear line between a random incident and a circumstance in which the victim’s personal freedom had been violated over an extended period.
The careful documentation and full preservation of test results in accordance with forensic protocols served not only the long-term treatment and recovery process for Felicia, but also provided a solid scientific foundation for re-evaluating the entire case, where her own body, through signs that could neither be fabricated nor appear by chance, had become the most compelling medical evidence of the involuntary nature of the 14 months.
She had vanished from her everyday life.
After the initial medical evaluations were completed and Felicia Lewis’s physical condition had been stabilized to a level that allowed for deeper intervention, she was moved into the phase of clinical psychological assessment, a step considered pivotal in determining her capacity to cooperate with the investigation as well as the safe boundaries for any subsequent contact.
Psychologists and psychiatrists assigned to work with Felicia followed a traumainformed care model in which the absolute priority was to avoid reactivating any of the harmful experiences she endured during the time she was missing.
Through multiple independent evaluation sessions combining behavioral observation, semi-structured interviews, and standardized testing tools, Felicia was diagnosed with complex post-traumatic stress disorder, a form of PTSD that commonly emerges in victims subjected to prolonged control, threat, and loss of autonomy.
Doctors noted that rather than reacting to a single event, Felicia’s nervous system had adapted to a state of chronic stress, resulting in hallmark symptoms such as hypervigilance, difficulty regulating emotions, feelings of detachment from reality, and disproportionate fear responses to seemingly harmless stimuli.
During assessments of memory and event recall, the specialists observed that Felicia’s long-term memory was not impaired in the sense of brain damage, but her ability to access memories directly related to the period of her disappearance was markedly fragmented.
When asked to recall events in chronological order, Felicia frequently paused, lost her train of thought, or exhibited physiological reactions such as trembling hands, increased breathing rate, and muscle tension, indicating that her autonomic nervous system was responding as though the threat remained present.
The experts concluded that these memory gaps were not the result of deliberate avoidance or fabrication, but rather a protective psychological mechanism in which the brain temporarily blocks access to experiences that carry a high risk of emotional overload.
On that basis, Felicia’s capacity to provide detailed, continuous, and consistent testimony was assessed as severely limited at this stage, particularly if questioning, followed in confrontational format, or demanded direct reconstruction of events.
The psychological reports emphasized that pressuring Felicia to recount specific details could not only fail to produce reliable information, but might also worsen her disorder, potentially leading to psychological freezing or complete loss of cooperation.
During observations of natural behavior, the specialists documented numerous characteristic fear reflexes tied to a sense of being controlled, including strong reactions when a door closed suddenly, when someone stood too close behind her, or when small changes in the surrounding environment occurred without prior notice.
These reflexes were recorded not as general anxiety manifestations, but as traces of a long period spent living under constant surveillance and loss of decision-making power, where seemingly neutral elements had once been linked to danger or punishment.
The experts also noted that Felicia tended to seek permission even in situations that did not require it, a behavior commonly seen in victims accustomed to having every personal action controlled by others.
From these evaluations, the professional team issued clear recommendations to the investigating agency, do not conduct direct interrogations using traditional methods, do not employ rapid pacing techniques, confrontation, or leading questions, and do not ask Felicia to confirm or deny investigative hypotheses at the present stage.
Instead, the proposed strategy was to gather information indirectly through objective data while conducting supportive psychological sessions in which Felicia retained full control over the extent, timing, and manner of what she chose to share.
The specialist stressed that any information Felicia provided in a stable, non-trauma activated state, even if fragmented or incomplete, held far greater value than detailed statements given under psychological pressure.
The psychological evaluation report concluded that Felicia was currently not in a condition suitable for participating in a confrontational investigative process.
But this did not mean she could not play a central role in clarifying the truth about the time she was missing.
On the contrary, respecting her psychological boundaries, establishing a sense of safety, and gradually restoring her sense of autonomy were seen as the prerequisite conditions for any meaningful cooperation to occur in the future.
For law enforcement, these assessments compelled a strategic adjustment in approach, requiring acceptance that progress in clarifying the case could not rely on direct victim testimony in the short term.
Instead, the investigation would have to be built in parallel from independent sources of evidence while allowing Felicia to gradually regain control over her own psychological state.
Faced with the objective facts that had been established, the authorities decided to restart the investigation by setting up a new interdisciplinary working structure in which every decision was based on verifiable data rather than relying on the victim’s currently unstable account.
A dedicated investigative task force was formed, including personnel from the Pierce County Sheriff’s Office, Yakima Police, representatives from the Ranger Service that had overseen the Mount Reineer Edge area, digital data analysis experts, financial investigators, and victim support personnel, ensuring that each information stream was handled by the appropriate specialized expertise, and that no duplication of effort occurred.
An internal coordination mechanism was designed around a central data hub model where every finding was uploaded in real time to a shared system for cross-referencing, minimizing the risk of developing disconnected hypotheses in parallel with strengthening the local team.
The task force conducted in-depth consultations with federal agencies experienced in handling cases involving abduction and human exploitation, including the Federal Bureau of Investigation and the Department of Homeland Security in order to access federal databases, behavioral analysis models, and federal tracking tools that were not available at the county level.
These consultations focused on standardizing the analytical framework, identifying specific indicators of intentional abduction behavior, and recognizing signs of prolonged but concealed exploitation rather than seeking confessions or descriptive details from the victim.
Based on the interdisciplinary discussions, the investigative direction was clearly defined as kidnapping and underground adult industry in the broad legal sense, emphasizing elements of control, forced movement, and long-term exploitation, while ruling out random event scenarios that did not align with the objective evidence already recorded.
Establishing this direction did not mean affirming the scale or structure of the criminal conduct.
Rather, it served as an analytical lens to prioritize resources and organize data according to the patterns with the highest likelihood of occurrence.
From there, investigative tasks were assigned along independent data axis.
One subgroup reanalyzed movement and vehicles, reviewing traffic cameras, parking lot data, secondary roads, and long-d distanceance public transportation schedules.
Another subgroup handled telecommunications data, re-evaluating mobile signals, cell towers, and the possible existence of intermediary devices in the relevant area and time frame.
The financial subgroup focused on money flows, card transactions, secondary accounts, cash activity, and signs of financial control.
While the behavioral analysis subgroup cross-referenced documented criminal operating patterns in the region with matching characteristics, each subgroup was required to compile a list of hypotheses based solely on its own data and present them according to falsifiability criteria, ensuring that every conclusion was independently verifiable.
The core operating principle agreed upon was data leads the way.
Meaning every step forward had to originate from confirmable quantitative or qualitative evidence with no direct confrontational questioning of the victim and no use of fragmented accounts to fill gaps.
This approach allowed the task force to pursue multiple parallel lines of analysis without exerting psychological pressure on the victim while also avoiding the risk of confirmation bias from clinging to a single hypothesis.
To ensure progress and discipline, a new investigative timeline was established with specific evaluation milestones starting from the point of Felicia’s reappearance and working backward along data trails.
Each milestone having clear completion criteria and an independent review mechanism.
Regular coordination meetings were scheduled to synthesize findings, eliminate redundancies, and adjust priorities as needed, while data access was tiered to protect sensitive information.
Performance metrics were applied not based on the number of statements obtained, but on the degree to which the scope of suspicion was narrowed, the ability to rule out incompatible scenarios, and the quality of cross-referencing between data sources.
By restarting the investigation under this structure, the authorities aimed to shift the focus from seeking subjective explanations to constructing an objective picture in which every finding was anchored in evidence and could withstand legal scrutiny.
Although no specific conclusions had yet been reached within this framework, the establishment of the interdisciplinary task force, federal consultations, clear investigative direction, and datadriven task assignments had created a tightly integrated operational foundation allowing the process to proceed in a systematic cautious manner appropriate to the complexity of the case.
While the investigative process was being restructured to rely entirely on objective data, another information channel gradually formed cautiously and under controlled conditions through indirect facts that Felicia Lewis could provide during supportive psychological sessions, not as formal testimony, but as fragmented pieces of information that emerged when she felt safe enough to speak.
The specialist noted that Felicia did not recount events in sequence.
Instead, details appeared intermittently, often tied to sensations, vague images, or pivotal moments.
And it was these puzzle pieces that the investigative team accepted as raw data requiring independent verification.
From those discontinuous descriptions, several consistent elements began to emerge.
First was the clear realization that in the initial days after her disappearance, Felicia had not remained within the Mount Reineer area or nearby regions as previously assumed.
Instead, she was moved continuously by road vehicle in a state where she had no control over the journey.
Although she could not pinpoint exact intermediate locations, Felicia repeatedly mentioned an unusually prolonged sense of time during travel, overnight stretches on the road, and distinct changes in the surrounding environment, details consistent with being taken out of state very early in the period following her disappearance.
This assessment was reinforced by her descriptions of unfamiliar road signs, different climate, and unfamiliar local accents she heard during rare moments of alertness, even though she could not attach them to specific place names.
for the investigative group, confirming the likelihood that Felicia had been transported out of state was pivotal, as it explained why the initial localized search efforts yielded no results and significantly expanded the scope of data that needed to be reviewed.
In the non-interrogative working sessions, Felicia also referred to the existence of one person she perceived as the primary coordinating figure, not the most frequently present individual, but the one with decision-making authority and overall control of the context in which she was placed.
Felicia’s description of this person did not focus on detailed physical appearance, but emphasized a sense of power, a commanding presence, and the way others appeared to follow his orders without question.
The manner in which she spoke about this figure, revealed a clear hierarchical structure, where control was not exerted through overt violence, but through coordination, indirect threats, and the ability to determine others fates, characteristics commonly seen in organized exploitation models.
Another significant detail Felicia shared concerned her escape, not as a spontaneous act or one aided from outside, but as the consequence of a series of small changes in the controlled environment, where a temporary lapse in direct supervision created a rare opening.
Felicia described that the moment did not come with a clear plan or prior preparation.
It was instead a survival response to a brief opportunity in which instinct overrode long accumulated fear.
The escape did not happen quickly or decisively, but was a high-risk process in which Felicia had to move without specific direction, relying solely on the drive to get as far as possible from the controlled space until she reached public transportation.
These descriptions, though lacking details about locations, held great value in identifying that the control mechanism had weakened at the decisive moment, thereby helping the investigative team infer aspects of the operational structure and the links within the related system.
In the process of synthesizing these indirect facts, one name began to appear with enough frequency to be recorded as a noteworthy lead, Leon Collins.
Felicia did not make direct accusations or provide detailed descriptions of this person’s legal role, but her reaction when the name was mentioned, along with linking it to the coordinating figure she had previously described, caused both the psychologists and investigators to regard this as information of particular weight.
The recording of the name Leon Collins was done carefully without confrontation and without asking Felicia to reconfirm to avoid creating pressure or distorting her already fragmented memory.
For the investigative group, this name became a new variable requiring independent verification and was immediately entered into the data cross referencing system.
Analysts began reviewing records related to human trafficking, labor exploitation, and similar activities documented across multiple states, searching for matches in names, aliases, operating patterns, and associated networks.
Initial cross-checking showed that Leon Collins had appeared in scattered intelligence files, not as an officially charged suspect, but as a person of interest in prior investigations that lacked sufficient evidence for prosecution, a pattern consistent with the indirect coordinating role Felicia described.
The fact that Felicia’s indirect information aligned with existing data in the system, even if incomplete, created a crucial intersection between the victim’s personal experience and the broader data picture the investigative team was building.
However, investigators unanimously agreed that this information should only be used as an analytical guide, not as conclusive evidence, and every hypothesis involving Leyon Collins had to be bolstered by independent data before any further legal steps could be taken.
In that context, Felicia’s role during this phase was not that of a witness providing a complete statement, but rather a source generating initial signals where fragmented pieces of information when placed side by side and cross-referenced with objective data began to shape a more specific investigative direction regarding what had happened during the time she was taken away from her former life.
From the moment the name Leon Collins was recorded as a lid requiring independent verification, the tracing operation was elevated to the federal level with the focus on cross-matching data in shared systems to determine whether this individual appeared in other investigative files.
Analysts conducted a review of identification data, residency history, vehicle records, related business information, and transaction traces previously logged in the centralized databases of the Federal Bureau of Investigation and the Department of Homeland Security.
Prioritizing items linked to federal jurisdiction matters such as interstate travel, use of intermediary identities, or operations spanning multiple jurisdictions.
Initial matching results showed that Leon Collins was not an entirely unfamiliar name in the system, even though it was not tied to any finalized criminal conviction.
Instead, the name appeared sporadically in intelligence analysis reports, unfinished investigations, and behavioral monitoring files showing indicators of human exploitation where the recorded role was typically coordinating rather than direct.
From this foundation, the interdisciplinary team shifted to analyzing interstate travel patterns in search of overlaps between time frames relevant to Felicia Lewis and documented activities of Leon Collins.
By aggregating vehicle data, fuel receipts, federal traffic camera footage, and long-d distanceance public transportation schedules, the analyst constructed a time resolved movement map that allowed identification of frequently used routes and recurring intermediate stops.
The analysis revealed a prominent movement axis forming along the Washington, Oregon, Nevada corridor, not as a single continuous trip, but as a series of segmented journeys where legs involved vehicle changes and were obscured through lowprofile transfer points.
The repetition of this axis across multiple separate files, not only those connected to Leon Collins, but also cases with similar characteristics, led to its assessment as a deliberate operational route rather than random coincidence.
When cross-referenced with the timeline of Felicia’s disappearance against established movement markers, the analysts noted a correspondence during periods when activity along the Washington, Oregon, Nevada axis was elevated, including clusters of short consecutive trips rather than one long haul, a pattern often employed to reduce traceability.
In addition to movement data, the analysis team linked to similar cases documented over multiple years, focusing on instances of adult disappearances in public settings with no physical traces left at the scene and reappearance in debilitated condition after a prolonged absence.
When these files were placed side by side, they displayed notable similarities in initial approach methods, timing of removal, transportation modalities, and indirect control structures, even though each case had its own unique context.
In several instances, Leon Collins or similar name variants appeared as a person of interest in scattered investigative reports, not sufficient for prosecution, but enough to form a pattern when analyzed networkwide.
Linking these cases was not intended to merge them into a hasty conclusion, but to construct a relational map showing how individuals, vehicles, and routes could interconnect over time.
From there, the hypothesis of a federally relevant human exploitation network gradually took shape, not based on a single piece of evidence, but on the convergence of multiple independent data layers.
This hypothesis described a distributed structure in which central coordinating roles were separated from direct contact operations, allowing those at the top to minimize legal exposure while maintaining control through intermediary networks.
Experts noted that this model aligned with Leon Collins appearing as a familiar name yet rarely facing prosecution since activities were sufficiently fragmented to evade direct attribution of responsibility.
Throughout the federal tracing process, every finding was cross-cheed against diverse data sources to ensure independence and hypotheses were retained only after passing rigorous falsification criteria.
The identified roads continued to undergo deeper analysis to locate fixed stopping points, short-term lodging facilities, and businesses potentially serving as intermediaries, while financial data was used to detect recurring transactions tied to movement timelines.
The tracing effort did not prioritize rapid establishment of criminal charges, but aimed to build a comprehensive picture of how a potential network operated, where Felicia Lewis might represent only one of many victims.
By the end of this phase, although no official legal conclusion had been reached, the convergence of federal data, interstate travel analysis, the Washington, Oregon, Nevada axis, and similar cases had created a sufficiently robust hypothesis framework, laying the groundwork for transitioning from data analysis to more targeted investigative actions within federal jurisdiction.
Based on the established transportation routes and connections at the federal level, the investigative team shifted its focus to identifying specific locations that were likely used to hold Felicia Lewis for extended periods under the assumption that control was not exercised at a single fixed facility, but rather through scattered properties sharing similar operational characteristics.
First, specialists reviewed the entire portfolio of real estate directly or indirectly linked to Leon Collins, including personally titled residences, properties held under intermediary legal entities, short-term lease agreements, and sites previously used as warehouses, workshops, or temporary lodging facilities.
The review extended beyond official ownership records to include powers of attorney, subleas contracts, and financial connections that could conceal actual control.
Since in organized exploitation models, coordinators typically avoid direct title ownership to minimize legal risk.
From an initial list of dozens of sites scattered along the Washington, Oregon, Nevada corridor, the investigative team applied screening criteria to narrow the scope, prioritizing properties located far from densely populated residential areas with high degrees of isolation, and minimal natural surveillance from surrounding communities.
Factors such as limited access roads, significant distance from major transportation routes, absence of public cameras, and a history of short-term tenant turnover were considered key indicators of potential concealment of internal activities.
When assessing isolation levels, terrain and security experts conducted analyses of satellite imagery, cadastral map data, and aerial photographs to identify parcels with structures suitable for restricting visibility and sound while allowing discrete control of entry and exit points.
Many locations were noted as renovated warehouses, small farms, or suburban homes with detached outbuildings, types of properties that attract little attention yet provide sufficient space to sustain long-term operations without drawing neighbors interest.
The investigative team paid particular attention to sites showing signs of minimal self-sufficiency, such as wells, generators, or large storage sheds, as these elements enable independent operation over extended periods without frequent external interaction.
When cross-referencing these characteristics with medical records and indirect evidence already obtained, several locations emerged as consistent with a non-traditional detention model.
One where control relies not on overt force or obvious confinement facilities, but on isolation, information restriction, and complete dependence on the controller.
Experts noted that this model allows sustained control over long periods without generating easily detectable signs of violence.
while simultaneously reducing the victim’s ability to seek external help.
From the narrowed list, the investigative team evaluated each site using a risk scoring scale that combined financial ties to Leon Collins, geographic suitability, and alignment with the established movement timelines.
High priority sites were incorporated into an on-site approach plan carefully developed to ensure participant safety and avoid compromising the investigation.
This plan included analyzing activity patterns in the surrounding areas, identifying low traffic time windows, and positioning discrete surveillance teams to gather additional intelligence before any overt action.
Approach methods were designed to be flexible, allowing adaptation to real-time conditions at each site from direct entry to prolonged surveillance aimed at confirming internal activity levels.
In parallel with on-site preparation, the legal team compiled necessary documentation to secure search warrants with every request required to be supported by a chain of reasoning grounded in objectively collected data, including financial linkages, movement analysis, and compatibility with the identified detention model.
Warrant applications were pursued on a sightby-sight basis rather than bundled to preserve constitutionality and reduce the risk of denial.
due to insufficient probable cause.
Prosecutors involved in reviewing the files emphasized the need to clearly demonstrate that each location not only had connections to Leon Collins, but also held a reasonable probability of containing evidence related to the control and exploitation of individuals.
During preparation, investigators were instructed to avoid any direct contact with persons associated with the target properties to prevent tipping off intentions and facilitating evidence destruction.
All preparatory steps and assignments were continuously updated in the central coordination system, ensuring that once formal search warrants were issued, enforcement teams could deploy immediately according to the pre-established script, approaching target locations in a synchronized, safe, and fully legally compliant manner.
On that basis, scene examination operations were activated simultaneously at multiple pre-identified locations, shifting the investigative focus from analysis and containment to the direct collection of physical evidence and digital data with the objective of objectively and independently reconstructing the mechanism of control and exploitation independent of Felicia Lewis’s account.
As soon as law enforcement reached the relevant properties, the first priority was to preserve the scene in its current state and secure electronic data sources because experts assessed that surveillance and digital storage systems could provide objective evidence of timing, frequency, and internal operational patterns.
at multiple sites.
Technical teams seized standalone surveillance camera systems disconnected from public networks, including DVR units, external hard drives, and storage devices installed in outbuildings, indicating that the monitoring was not for conventional security purposes, but for internal control.
Accompanying electronic data such as laptops, old cell phones, memory cards, and portable storage devices were sealed and immediately transferred to a digital forensics laboratory for extraction under chain of custody protocols with the goal of recovering access histories, contact lists, and deleted files.
In parallel with digital data, investigators discovered numerous discreetly stored paper documents, including handwritten ledgers and encoded work schedules using symbols that did not overtly reveal their purpose on the surface, but exhibited repeating structures by day and by group.
These ledgers recorded fixed time slots, recurring symbols, and lists of abbreviated names indicating the existence of an organized visitor schedule managed on a cyclical rather than random basis.
Cross-referencing the timestamps in the ledgers with camera data and movement records showed a high degree of compatibility, reinforcing the conclusion that these documents were not miscellaneous personal notes, but tools for coordinating operations.
During the interior scene examination, forensic teams collected biological samples according to standard protocols, focusing on high contact surfaces and secluded areas deliberately designed to limit visibility.
Initial collection results revealed the presence of DNA from multiple different individuals far exceeding the number of legally residing or regularly present persons according to administrative records.
a strong indicator that the location had been used by many people over overlapping periods.
These samples were cataloged, sealed, and sent for independent analysis to determine the number of distinct individuals, persistence times, and possible links to other missing persons files in the system.
In addition, investigators documented physical signs indicating organized activity beyond ordinary household or business use, including functional spatial divisions, cyclical cleaning, and item replacement procedures, and the presence of hospitality related items that were centrally stored and tightly controlled.
These indicators when placed alongside the recorded schedules and surveillance data formed a picture of a structured operation in which people were brought into and removed from the space according to a controlled timetable.
Particularly the discovery of security items, secondary locks, and concealed passageways showed deliberate efforts to restrict external access and observation consistent with the non-traditional confinement model identified in prior analysis.
Throughout the documentation process, investigators emphasized recording the scene in a neutral manner, detailed, but avoiding speculation so that all conclusions could rest on independent verifiable evidence.
Every finding was photographed, measured, and marked with precise locations, enabling forensic reconstruction of the space and sequence of activities.
When viewed holistically, the collected evidence not only showed signs of organized exploitation activity, but also reflected a durable, time-tested operational system in which data, scheduling, and spatial control were tightly coordinated to maintain dominance without overt violence.
More importantly, the entire chain of evidence stood firm without relying on direct testimony from Felicia, fulfilling the strategic objective of building an independent case file in which the truth is established through data, physical traces, and scientific analysis.
Prosecutors overseeing the examination process assessed that the level of evidentiary convergence from cameras, paper documents, DNA to spatial structure met stringent standards for relevance and probitative value, allowing reconstruction of activities over time and identification of Leon Collins coordinating role without requiring the victim to confront traumatic memories directly.
The scene examination, therefore, was not merely a step in evidence collection, but a process of transforming hypotheses into concrete data, strengthening the legal foundation of the case with objective evidence capable of withstanding independent scrutiny.
Based on all the physical evidence, digital data, and behavioral analysis collected from the related locations, the investigative team conducted a systematic synthesis step to clarify the criminal motus operandi that was employed not as an individualized reconstruction, but as an operational model capable of being repeated against multiple different victims.
First, the approach and victim selection demonstrate that this was not random or opportunistic behavior, but a deliberate selection process based on degrees of vulnerability within the context of everyday life.
The identified victims were adults with stable routines, not belonging to traditionally high-risk groups.
Yet they had periods of traveling alone in public spaces with minimal supervision and no companions, creating opportunities for initial contact without arousing suspicion.
The chosen contact settings typically occurred at transitional locations such as parking lots, transfer stations, or urban fringe areas where the presence of strangers did not trigger clear warning signals.
This analysis shows that the approach tactic was designed to blend into normal social interactions, avoiding any overt coercive signs from the outset, thereby reducing the likelihood of immediate victim resistance or helpseeking.
After successful initial contact, the transportation and control methods were implemented according to a segmented model in which the victim was not moved in a single continuous journey, but through multiple short legs with changes in vehicles and stopover points intended to disorient and sever spatial orientation capabilities.
Movement data reveal the alternating use of personal vehicles, short-term rentals, and long-d distanceance public transportation, a tactic that disperses traces and reduces the feasibility of continuous tracking.
During this process, control did not rely on overt violence, but on information restriction, creating dependence on the person directing the journey, causing the victim to gradually lose self-determination even in basic choices.
Once removed from familiar environments, the mechanism for maintaining dependence was activated, not through traditional confinement, but through social isolation, control of daily rhythms, and the creation of a perception that compliance was the only path to relative safety.
Behavioral analysis experts concluded that this model exploits human survival reflexes where the victim adjusts behavior to minimize risk in uncertain circumstances gradually developing a state of psychological and behavioral dependence.
This dependence was reinforced by cyclical repeating elements from scheduled routines to unspoken rules that were not clearly explained but consistently enforced making it difficult for the victim to recognize opportune moments to attempt escape.
In the overall picture, Leon Collins coordinating role emerges not as the direct perpetrator of every act, but as the central decision maker and resource allocator responsible for connecting the links in the operational chain.
Data analysis shows that Leon Collins rarely appeared at initial contact points or specific scenes.
Instead, he maintained indirect presence through directives, schedule arrangements, and information control, a strategy to minimize the risk of direct identification.
This role allowed him to retain overall control while maintaining distance from actions that could constitute direct evidence while simultaneously creating a legal buffer through intermediary individuals.
Seized documents and data indicate the existence of a flexible hierarchical structure where orders were transmitted in a one-way direction and responsibility was dispersed, complicating individual accountability if only isolated acts are examined.
When placing these elements within the federal legal framework, the prosecution team proceeded to identify the constituent elements of federal crimes, including interstate kidnapping, use of interstate facilities for transportation, and maintenance of human control through indirect threats and coercive dependence.
The interstate movement proven by transportation and telecommunications data meets federal jurisdiction criteria while the prolonged and organized exploitation model satisfies the legal definitions of deprivation of liberty and human trafficking under current statutes.
The analysis also emphasized that the absence of overt violence or traditional confinement does not diminish the criminal nature of the conduct.
On the contrary, it demonstrates a high level of sophistication in evading detection and prosecution.
In summary, the criminal motus operandi is identified as a deliberate chain of actions designed to integrate into normal social life, exploit surveillance gaps and victim psychological reflexes while operating through a distributed structure to sustain control over extended periods.
This approach enables the investigative and prosecutorial teams to view the case not merely as an isolated incident but as a concrete manifestation of a repeatable federal level criminal model in which analysis of the modus operandi plays a pivotal role in establishing criminal responsibility at the highest level without relying on direct victim testimony.
From the analysis of the criminal motus operandi at a structural level, the investigative team continued to dissect the unethical operational mechanism run as a closedloop system in which control was not based on a single measure, but on a combination of multiple layers designed to gradually strip away the victim’s autonomy.
One of the first steps identified was the confiscation of identification documents and personal means of recognition.
Not only to prevent independent movement, but also to undermine the victim’s sense of legal existence within society, making it difficult for them to access official assistance even when an opportunity arose.
The absence of documents created a state of complete dependence on the controller in every situation involving travel, medical care, or external communication while simultaneously heightening the fear of detection or reprisal if the victim attempted to seek help on their own.
In parallel, the threat mechanism was deployed indirectly, focusing on the safety of family and loved ones rather than overt violence, a tactic particularly effective against victims with clear family responsibilities.
Implied reminders, collected personal information, and demonstrated access to the private lives of relatives were used to instill the perception that any act of resistance could lead to consequences beyond the victim’s control.
The analysis experts assessed that this form of threat sustained compliance more durably than direct violence because it shifted the burden of risk from the individual victim to those they wish to protect, paralyzing the capacity for resistance over an extended period.
Alongside psychological pressure, financial and mobility control played a central role in maintaining dependency.
All sources of income, spending, and means of transportation were centrally managed, leaving the victim unable to accumulate resources or plan an escape.
Funds generated from exploitation activities were not handed over directly, but recorded internally as a form of living expenses or debt to be repaid, creating a vicious cycle in which the victim remained perpetually in deficit and dependent.
Movement between locations did not occur randomly, but was scheduled flexibly, allowing victims to be rotated according to demand while preserving traceability difficulty.
Victims were not kept at one site for too long, reducing the chance of forming social connections or gaining sufficient familiarity with the terrain to find a way out while also blurring temporal traces when cross- refferenced with conventional search efforts.
This rotation mechanism also enabled optimization of exploitation by region and timing where shifting demand was met through rapid relocation without the need to expand fixed facilities.
Maintaining the network across multiple states was achieved through a distributed structure in which operational sites, transportation means, and intermediary individuals were replaced flexibly, minimizing risk if any single link was exposed.
Interstate movement routes served not only concealment purposes but also provided legal advantages to coordinators as fragmenting activities by jurisdiction made it difficult for local agencies to recognize the full picture without federal coordination.
In this model, victims became mobile elements whose positions were adjusted according to market demand and safety levels while the central coordinating structure maintained connectivity with minimal direct presence.
Experts noted that it was precisely the combination of document control, indirect threats, financial management, flexible rotation, and multi-state operation that created a resilient system where coercion did not need to be overt yet remained effective over long periods.
When placed in the context of the case involving Felicia Lewis, the investigative team concluded that every element aligned with the federally defined model of organized sensitive service business, not only because of the exploitation behavior, but due to the systematic manner of stripping freedom and controlling individuals.
This mechanism analysis allowed the separation of the victim’s personal experience from the broader operational structure, enabling investigators and prosecutors to build arguments based on patterns and data rather than relying on detailed traumladen descriptions.
At the same time, it clarified that the victim’s silence, compliance, or surface level cooperation could not be interpreted as consent, but was instead the outcome of a system deliberately designed to sustain dependency through multiple layers of sophisticated control, spanning space and time, sufficient to make escape a rare and highly risky act.
After the operational mechanism of the disguised sensitive service network was established through independent evidence and the coordinating structure had been clarified, the authorities moved into the action phase with the objective of isolating the central coordinator from the rest of the system, treating the arrest of Leon Collins as the pivotal step to halt continued operations and prevent evidence destruction.
The plan was built on tightly coordinated efforts between federal and local forces with each unit assigned a specific role to ensure legality, safety, and effectiveness from surveillance and execution to evidence preservation.
This coordination did not proceed hastily.
It was prepared over many weeks through discrete tactical rehearsals, analysis of the suspect’s daily routines, travel schedules, and still active connections in order to select an intervention window that minimized risk to participating personnel as well as the surrounding community.
The arrest warrant was issued on the basis of a thoroughly vetted case file in which the chain of evidence was presented in logical data sequence demonstrating Leon Collins central coordinating role in the control, movement, and exploitation of individuals across multiple states meeting the strict criteria for federal jurisdiction.
Execution of the arrest warrant took place at a time assessed as having the lowest likelihood of external interference when the suspect was in his primary residence with no signs of imminent movement, allowing rapid approach and control of the situation in a short time frame.
When the executing units moved in simultaneously, Leon Collins was subdued without confrontation, reflecting tactical calculations designed to avoid any unnecessary escalation.
Immediately following the arrest, the suspect was separated from personal communication devices, cell phones, and digital equipment were sealed on site to prevent the sending of warning signals to remaining network links.
In parallel with transporting the suspect, search teams were deployed at Leon Collins primary residence within the scope of the approved warrant, focusing on seizing documents, electronic devices, and any evidence that could further substantiate the already identified coordinating role.
The search was conducted according to strict forensic sequence.
Each room and area was documented in its current state before collection to ensure evidence integrity and usability in subsequent proceedings.
At the residence, authorities seized additional digital storage devices, handwritten records, and backup communication means indicating a level of preparation to maintain operations even if one channel was disrupted.
These documents were not ostentatious, but were stored in dispersed locations consistent with the discrete operational model previously analyzed.
Certain items recovered showed direct links between Leon Collins residents and properties previously used as confinement sites, thereby reinforcing the chain of evidence regarding actual control over those spaces.
During the search, investigators placed particular emphasis on preserving digital data, employing on-site backup techniques to avoid information lost due to encryption or selfdeion mechanisms, while sealing devices according to proper protocol for forensic analysis.
The additional evidence seized was not only intended to strengthen the case against Leon Collins personally, but also to expand the ability to identify and neutralize remaining network links.
Since isolating the central coordinator would only be effective if information flows and directives were completely severed.
Therefore, immediately after the arrest, federal agencies implemented emergency measures to monitor the systems reaction, including surveillance of unusual transactions, communications, and movements that might arise when the network lost its command point.
Leon Collins was transferred to a highsecurity federal detention facility, isolated from individuals with whom he had direct prior contact to prevent remote coordination or influence over potential witnesses.
This isolation served not only a security purpose, but also a strategic one, weakening the network structure, as Leon Collins coordinating role depended heavily on maintaining realtime communication and decision-making capability.
In internal reports, law enforcement recorded that the arrest proceeded exactly according to plan with no unforeseen incidents and no impact on community safety, an important factor in cases of federal scope.
However, investigators also stressed that the arrest of Leon Collins was not regarded as the end of the process, but as a necessary step to shut down the operational hub and ensure that remaining evidence could be collected without interference for the case file.
The simultaneous arrest and search actions created a clear shift from the analysis and pattern establishment phase to the legal enforcement phase where hypotheses were transformed into concrete court authorized actions through multi-level coordination.
In that context, isolating Leyon Collins from the network served not only to prevent continued coordination or interference with the evidence stream, but also established a distinct break between the investigative action phase and the legal processing phase, where all collected data could be reviewed, standardized, and reorganized under prosecutorial standards.
From the moment the suspect was fully subdued and external interference risks were eliminated, the focus of the case naturally shifted to the legal process as federal prosecutors officially took over the file, marking the transition to the prosecution phase for the interstate and organized conduct established through independent evidence.
Based on the chain of data collected from scene examinations, financial analysis, telecommunications, and movement records, Leon Collins was indicted under federal law with jurisdiction clearly established due to elements crossing state lines, use of interstate facilities, and long-term control over individuals.
The formal charges announced included federal kidnapping, conspiracy to transport and control persons for purposes of exploitation, maintenance of an organized exploitation network along with ancillary offenses related to money laundering, obstruction of justice, and use of interstate facilities to commit crimes.
The charges were presented through a detailed indictment in which each count was tied to a distinct set of evidence, allowing the court and defense to directly cross-reference the original data without relying on subjective interpretation.
In this prosecutorial structure, Felicia Lewis’s role was clearly defined and limited from the outset, consistent with the medical and psychological recommendations already documented.
She was not positioned as a central witness required to reconstruct the entire sequence of events, but participated only to the minimum extent necessary to confirm elements that could not be replaced by other evidence.
Prosecutors emphasized that their strategy did not depend on detailed testimony from Felicia in order to avoid further harm to the victim while ensuring the case files robustness against any legal challenge.
Instead, Felicia’s limited statements were used as confirmatory context for the overall nonvoluntary nature of the control behaviors.
While the core burden of proof rested on objective data, movement schedules, financial structures, surveillance systems, coordinating documents, and biological samples collected from the scenes.
The prosecution strategy was built around a datadriven case approach in which timelines were presented as a closed logical sequence, allowing the jury to follow the network’s operational process without exposure to graphic or traumatic descriptions.
Each alleged act was linked to specific cross-verified evidence from multiple sources to eliminate the possibility of reasonable alternative interpretations by the defense.
At the same time, prosecutors prepared rebuttals to anticipated defense strategies, including denial of the coordinating role, shifting blame to intermediary individuals, or claims that victims participated voluntarily.
To counter these, the prosecution file focused on proving the systematic mechanisms of control and dependency, demonstrating that apparent voluntariness could not exist in a context of prolonged document deprivation, movement restriction, and indirect threats.
During the pre-trial preparation phase, prosecutors worked closely with digital forensics teams and behavioral analysts to transform technical data into court accessible presentations, including network diagrams, movement maps, financial flowcharts, and visualized timelines that clearly illustrated Leon Collins central coordinating role.
Witness selection was conducted selectively, prioritizing experts capable of explaining data in a neutral and persuasive manner rather than relying on emotional narratives.
Victim and witness protection measures were maintained throughout, including restrictions on media contact and control of public information to ensure the proceedings were not influenced by public opinion or external pressure.
In parallel, the prosecution pursued pre-trial procedures to exclude irrelevant evidence, affirm the constitutionality of the search and arrest warrants, and verify the chain of custody for all evidence, ensuring that every piece presented in court met stringent legal standards.
Initial hearings focused on the scope of the indictment and jurisdiction during which the court acknowledged the consistency of the file and permitted the case to proceed to trial on all stated federal charges.
For Felicia, this preparation occurred within a context of continuous protection and support where she was not required to participate in unnecessary procedures reflecting the justice systems commitment to balancing the demands of justice with the responsibility to protect victims.
The legal progression of the case was shaped by a consistent strategy, constructing the indictment around operational structure and objective data while minimizing reliance on trauma laden testimony, thereby forming a sufficiently rigorous file to enter the federal trial phase without expanding the scope of debate into emotional details.
On that foundation, the formal proceedings officially moved into the courtroom when the federal trial opened with a jury selected in full accordance with procedure, fully reflecting the gravity of the case and Leon Collins’s individual criminal responsibility within an organized exploitation network that crossed state lines.
During the trial, the prosecution presented the case in a tightly ordered sequence, beginning with proof of federal jurisdiction through interstate movement and use of federal infrastructure, then systematically clarifying Leon Collins’s coordinating role through independent chains of evidence, including telecommunications data, financial records, coordinating documents, and digital forensic results collected from multiple different locations.
Each group of evidence was presented not as isolated pieces, but as overlapping layers, demonstrating the existence of a stable operational pattern over time in which the defendant held the central decision-making role, allocating resources, and maintaining control without needing to appear directly at every site.
Expert witnesses were called to explain how these data sets interacted, helping the jury understand that the overlaps in timing, travel routes, and methods could not be explained by coincidence or independent activity of unrelated individuals.
The defense attempted to undermine that argument by emphasizing the absence of direct evidence, placing Leon Collins at specific scenes, and questioning the reliability of databased inferences.
But these challenges faced difficulty when the prosecution pointed out that the systematic absence from scenes was itself part of the coordinating strategy designed to evade direct liability.
Throughout the trial, Felicia Lewis’s role was kept to a minimum.
Consistent with the victim protection orientation, she confirmed only the essential elements related to nonvoluntary control, while the vast majority of the burden of proof rested on objective evidence, allowing the jury to focus on the criminal structure rather than personal details.
After both sides completed their presentations and arguments, the jury entered deliberations with clear instructions from the judge regarding the beyond a reasonable doubt standard and the elements of the federal offenses to be considered.
The deliberation process lasted several days reflecting the complexity of the file and the large volume of evidence as the jury had to evaluate not only each piece individually but also the interconnections among them as a whole.
Upon returning to the courtroom, the jury announced a unanimous verdict, finding Leon Collins guilty on the primary charges, determining that the evidence had clearly proven the defendant’s central coordinating role in an organized sensitive service business network operating across state lines.
At the sentencing hearing, the judge took time to analyze the severity of the conduct, emphasizing that this was not a series of isolated or impulsive violations, but a deliberately maintained system over a prolonged period, causing deep and lasting harm to multiple individuals while challenging law enforcement’s ability to detect it.
On that basis, the court sentenced Leon Collins to 45 years in federal prison, deeming this punishment necessary to fully reflect the nature and consequences of the criminal conduct, as well as the leadership and coordinating role the defendant had assumed.
The judgment explicitly stated that the defendant was not eligible for parole or sentence reduction under current guidelines, citing the ongoing risk of harm if released early and the need to protect society from criminal models with high recidivism potential.
At the same time, the court noted that although the verdict had concluded Leyon Collins’s criminal liability, the evidence presented showed that the sensitive service business network did not depend on a single individual, but was designed with a distributed structure capable of continuing even after one link was removed.
Therefore, in the sentencing decision and accompanying statements, the judge stressed the necessity of continuing investigation into other related individuals and entities regarding this judgment as an important but not final step in the pursuit of justice.
For the jury, reaching the guilty verdict was seen as an affirmation that sophisticated forms of human control and exploitation, even when they avoid overt violence and are concealed behind complex legal mechanisms, can still be exposed and addressed when evidence is collected, analyzed, and presented systematically.
The trial concluded in an atmosphere of order and somnity without explosive emotional moments, but it left a clear legal milestone.
The combination of data-driven investigation, a prosecution strategy focused on structure and a firm verdict had established criminal responsibility at the federal level while sending a message that human exploitation networks, no matter how sophisticated, remain within the reach of the justice systems light.
After the federal court’s verdict, the consequences for Felicia Lewis did not end with the sentencing, but began a prolonged, complex, and tightly managed recovery phase in which the top priority was long-term medical and psychological treatment aimed at stabilizing her physical condition and minimizing the accumulated effects from the entire period of control.
Doctors and mental health specialists designed a step-by-step protocol combining physical care, nutritional monitoring, functional rehabilitation, and intensive psychological therapy with the goal not to completely erase traumatic memories, but to help Felicia develop sustainable coping mechanisms that would allow her to function in daily life without being constantly dominated by fear reflexes.
This process required time and patience because the psychological impacts did not manifest uniformly.
There were periods that seemed stable, but also times when symptoms resurfaced when faced with seemingly harmless triggers.
In parallel with treatment, a major decision was made to change her active identity, including the use of new personal information for administrative, medical, and social transactions to ensure safety and reduce the risk of unintended recognition or contact.
This change did not mean erasing the past, but creating a necessary protective layer so Felicia could exist in public spaces without perpetual vigilance.
An element assessed as crucial for psychological recovery.
A direct consequence of that decision was that Felicia did not return to her old life.
She did not go back to her previous residence did not reconnect with the social relationships tied to the period before her disappearance because those spaces and old routines were identified as carrying a risk of triggering traumatic memories or placing her in prolonged states of unease.
Instead, her new life was designed with a narrow structured scope where daily activities were predictable and supported by professionals, allowing Felicia to gradually rebuild a sense of personal control that had been stripped away for so long.
Limited social contact was an unavoidable part of this phase, not out of a desire for isolation, but because of the need to protect psychological stability and personal safety.
Interactions were restricted to a small circle that included close family medical staff and a few carefully vetted support personnel.
Contact with media and the public was strictly limited, not only to safeguard privacy, but also to prevent the story from being rehashed in ways that could erode the recovery process since each retelling could trigger unexpected psychological reactions.
In that context, reintegration was not understood as a full return to social life, but as a controlled gradual expansion of activity range according to Felicia’s adaptive capacity under the supervision of psychologists and social advisers.
Reintegration milestones were set flexibly, not bound by rigid timelines, allowing adjustments whenever signs of overload or stress appeared, reflecting an approach centered on safety and sustainability.
Felicia was supported in developing new skills suited to her current circumstances, from stress management to building healthy daily routines in order to create a stable foundation before considering any further steps toward expanded social or occupational interaction.
Throughout this process, the specialists emphasized that recovery did not mean returning to the pre-disappearance state, but forming a new state of balance in which limitations were accepted as part of reality rather than viewed as failure or deficiency.
Felicia in her role as a surviving victim was given the power to choose the pace and scope of recovery instead of being pressured to demonstrate normaly according to societal expectations an element that had once made reintegration difficult for many other victims.
Support agencies noted that respecting this right to self-determination helped reduce the feeling of being controlled again, enabling Felicia to gradually rebuild trust in her surroundings.
The aftermath of the case, therefore, was measured not only by the harm that occurred, but also by what could never be returned, the permanently changed relationships, and a new life formed within stricter safety boundaries.
Yet within those very boundaries, the recovery process showed a quiet form of progress in which every small stabilization was regarded as an achievement, and simply existing, adapting, and maintaining daily life became the central goal, replacing grand expectations of a complete return to the past.
At the present time, the case is legally considered fully closed after the federal sentence against Leon Collins took effect, and no further appeals could alter the core criminal liability.
While all related procedural steps have been completed in accordance with due process, creating a clear end point in the justice system for the central file of the matter.
This closure not only marks the end of a prolonged and complex prosecution process, but also establishes a stable legal state for the victim and all involved parties where the risk of renewed intervention from the defendant has been eliminated.
However, the impact of the case did not stop at the courtroom.
It spread to the local community, especially in areas once regarded as safe and familiar, such as public parking lots, transit stations, and the edges of natural tourist zones.
Authorities noted a distinct shift in community perception.
Spaces previously assumed harmless are now viewed with greater caution, leading to increased surveillance measures, warning information, and coordination among local management units.
The case also triggered a wave of re-evaluation of missing person’s intake procedures and handling of reappearance cases because what occurred demonstrated that a victim’s return does not mean the matter is over.
On the contrary, it can open an entirely new investigative direction with broader scope and greater severity.
From an operational standpoint, the postreappearance investigation model stands out as a key highlight as law enforcement agencies drew the lesson that prioritizing objective data, physical evidence, and structural analysis can build a solid case file without placing the burden of disclosure on the victim.
This approach was deemed appropriate for cases involving deep trauma where personal accounts may be fragmented, limited, or incomplete.
Yet a large volume of data capable of reconstructing criminal behavior still exists if properly exploited.
Internal reports indicate that this model has been incorporated into training programs and referenced by other investigative units as a practical precedent for handling abduction and human trafficking cases when victims reappear after long absences.
On a broader level, the case serves as both a legal and operational precedent, proving that sophisticated forms of control and exploitation, not reliant on overt violence, can still be effectively prosecuted when the constitutive elements are proven through data and systematic analysis.
Federal prosecutors assessed that the verdict in this case helped clarify the application of federal law to distributed networks where the central coordinating role is not easily identifiable through traditional investigative methods.
At the same time, it reinforced the argument that a victim’s silence or surface level compliance cannot be interpreted as consent, a critical point in handling modern human trafficking cases.
For the community, the matter became a stark reminder of risks existing even in familiar public spaces where seemingly innocuous interactions can be exploited by individuals or networks with harmful intent.
Awareness campaigns were launched focusing on recognizing unusual approach signs, encouraging vigilance without inducing panic, and highlighting the importance of early reporting of suspicious behavior.
At the same time, park managers, parking facilities, and transit stations reviewed their security systems from surveillance cameras to staff presence to minimize the gaps that had once been exploited.
From a policy perspective, the case helped drive discussions on resource allocation for specialized human trafficking units, especially amid increasingly sophisticated and flexible networks that operate across multiple jurisdictions and employ hard to detect control methods.
Experts emphasized that the greatest lesson is not in one convicted individual, but in recognizing that such cases can persist long outside view, if only relying on outdated investigative templates.
Therefore, combining technology, data analysis, and a victim-entered approach is seen as the necessary direction moving forward.
Looking back at the entire process, the current status of the case reflects a fragile balance between closure and continuation.
Closure in the legal sense for the central defendant, but continuation in terms of awareness, prevention, and system improvement.
The matter left its mark not only in judicial records but also became a reference point for how society perceives human trafficking risks in public areas, reminding us that safety cannot be taken for granted and that the most familiar spaces sometimes need to be re-examined with clearer, more proactive eyes.
The story of Felicia Lewis reflects a reality very close to everyday life in the United States today.
The risk of human trafficking does not exist only in impoverished areas, high crime zones, or unusual circumstances.
It can begin right in familiar public spaces where people normally assume they are safe.
Felicia vanished from a parking lot near a busy tourist area under favorable weather conditions in broad daylight after a brief non-suspicious interaction.
This detail reminds us that danger in modern society often does not look violent or chaotic.
Instead, it hides beneath very ordinary interactions.
The first lesson is that vigilance does not mean paranoia, but it must be placed correctly.
Moments of traveling alone, transitional points like parking lots, bus stations, and urban edges are where risks most easily arise.
Second, the story shows that human trafficking crime today operates through psychological, financial, andformational control, not just violence.
So, the fact that a victim does not cry for help or does not escape immediately should never be misinterpreted as voluntary.
This carries major significance in how American society views and treats victims after their return.
As seen in the way Felicia was protected, shielded from media, and not pressured to recount traumatic details.
Another important lesson lies in the system.
The case was only clarified when authorities prioritized data, federal coordination, and did not place the burden of proof on the victim.
In real life, this underscores the community’s role in early reporting of unusual signs and supporting policies that strengthen surveillance, education, and victim assistance.
Finally, Felicia’s story does not teach us to live in fear, but reminds us that safety in modern society results from awareness, personal responsibility, and a system ready to listen, protect, and act promptly.
If the story of Felicia Lewis has helped you see more clearly the hidden dangers that still exist in everyday life in the United States, please subscribe to the channel so we can continue following and understanding more deeply the cases behind the silence.
Thank you for listening to the very end and see you in the next video with more true stories where the truth is not just to know but to warn and protect
News
Six Cousins Vanished from a Train Station in 1996 —27 Years Later FBI Found Their Bag
In 1996, six cousins vanished from a busy train station in broad daylight. No witnesses, no suspects, no goodbyes, just…
Florida 1955 Cold Case Solved — Arrest Shocks Community
In the summer of 1955, Llaya Merritt rode her bright colored little bike around the Sloan Avenue neighborhood, just a…
25 Students Vanished on a Field Trip in 1998 — 23 Years Later, the School Bus Is Found Buried
On the morning of April 12th, 1998, 25 high school seniors climbed aboard a bus for what should have been…
Two Officers Vanished From Their Patrol Car in 1993 — Clue Found in 2024 Turned the Case Upside Down
On a foggy October night in 1993, a sheriff’s cruiser was found parked on the shoulder of County Road 19…
Girl and Grandpa Vanished While Playing Outside — 15 Years Later They Find This Near the Old Shed…
In the summer of 1994, a quiet rural town in Ohio was shaken by the sudden disappearance of a grandfather…
Family Vanished on Road Trip in 1998 – 20 Years Later a Drone Makes A Chilling Discovery…
In August 1998, the Morrison family packed their car for what should have been a perfect week-long camping trip to…
End of content
No more pages to load